Here's a simple truth most Salinas businesses aren't being told about cybersecurity: generic advice like "use a firewall" or "watch out for phishing" is dangerously incomplete. This one-size-fits-all approach misses the unique threats facing our local industries, from agriculture in Salinas to hospitality in Monterey. It leaves you exposed to risks that big, national providers simply don’t see from a thousand miles away.
Why Standard Cybersecurity Advice Fails Salinas Businesses

If you run a business in Monterey County, you've heard the standard tips. Use strong passwords, keep your software updated, train employees to spot weird emails. It all sounds sensible, right? But that advice is the bare minimum.
It’s like telling a farmer to just "water the plants" without explaining anything about our specific soil types, local pests, or the complexities of drip irrigation. It skips over the details that actually matter right here in the Salinas Valley.
However, our research shows that most providers fail to address local industry-specific threats, outdated technology habits, or compliance issues relevant to Salinas-area businesses. This creates a massive, dangerous gap between what you think protects you and what actually will.
The Real Local Threat Landscape
From our experience on the ground, most IT providers are handing out checklists that fail to address the factors that truly affect businesses in Salinas, Carmel, and beyond. They see a generic "small business" but overlook the context that turns a theoretical risk into a costly, business-stopping reality.
What does that generic advice miss?
- Industry-Specific Gaps: A standard checklist won't mention the risks of unsecured IoT sensors on a farm or the specific vulnerabilities in a school's student information system.
- Deep-Rooted Tech Habits: Many local businesses still rely on older, on-premise servers. If not managed with an expert eye, these are prime targets for ransomware gangs.
- The Insurance & Compliance Squeeze: They don't prepare you for the incredibly strict cyber insurance requirements that are now non-negotiable for winning certain contracts.
The hidden vulnerability we see time and again is just how underprepared most Salinas-area businesses truly are. Recent data shows only 34% have a formal incident response plan developed by professionals. This leaves a staggering 27% without any cyber insurance and 33% relying on the business owners themselves for threat alerts—a recipe for disaster when attacks move in minutes, not days.
This is exactly where local, hands-on expertise becomes non-negotiable. At Adaptive, we don’t follow a script; we build security strategies that fit the operational realities of Salinas and Monterey businesses. It's also crucial to realize that many businesses operate under false assumptions about data security. Before you assume your old equipment is safe, it's worth debunking some of these common hard drive destruction myths to see how easily security gaps can form.
To build a defense that actually works, you have to first understand how cyber threats are evolving and what that means for us here at home.
The Myth That You Are Too Small To Be a Target
One of the most dangerous beliefs I hear from local business owners is, "We're just too small to be a target." It’s an understandable thought. The news is always filled with stories about massive corporate data breaches, so it's easy to assume cybercriminals are only interested in the big fish.
But that assumption is a costly myth, and it’s leaving countless Salinas businesses completely exposed.
To get why, you have to change how you picture a cybercriminal. Don't imagine a master thief in a dark room, carefully planning a high-stakes heist on a single corporate vault. Instead, picture an automated fishing boat dragging a massive net across the ocean floor. That boat isn't looking for one specific type of prize fish; its net is designed to scoop up anything and everything that can't get out of the way fast enough.
That’s exactly how modern cybercrime works. Attackers use automated programs that constantly scan the internet for weaknesses—not for company logos or revenue reports. These programs cast an incredibly wide net, hunting for simple weaknesses like unpatched software, easy-to-guess passwords, or outdated firewalls. They aren't searching for the biggest business, just the easiest catch.
Why Your Salinas Business Is Low-Hanging Fruit
Your size isn't a shield; in many cases, it actually makes you a more attractive target. Cybercriminals look for opportunities, and they know that smaller businesses often have smaller IT budgets, less sophisticated defenses, and no one on staff dedicated to security.
This combination turns your Salinas farm, Monterey restaurant, or Carmel boutique into what they call "low-hanging fruit."
Here’s a breakdown of what makes a small business so appealing to an attacker:
- Perceived Lack of Resources: They bet you don't have an enterprise-level security budget. This makes you a much softer target than a large corporation with a full-time cybersecurity team on high alert.
- Gateway to a Bigger Prize: Sometimes, your business is just a stepping stone. Hackers will compromise smaller, trusted vendors to gain access to their larger clients, using your network as a backdoor into a more valuable supply chain.
- Higher Likelihood of Paying Ransom: Criminals know that a small business can't afford days or weeks of downtime. They wager that you'll pay a smaller ransom quickly just to get your critical operations back online and avoid going under.
Many small business owners in Salinas believe they are too insignificant to be a target, a dangerous myth debunked by the reality that essential cybersecurity solutions for small businesses are a necessity, not a luxury. The truth is, your perceived insignificance is exactly what puts you in the crosshairs.
The Numbers Don't Lie
This isn't just a theory; the statistics are sobering. Small and medium-sized businesses (SMBs) right here in our community are facing an epidemic of cyberattacks.
A shocking 43% of all global cyberattacks are aimed at small businesses. Why? Because criminals see them as the path of least resistance. The consequences are devastating, with 60% of small companies going out of business within six months of being victimized.
This widespread misunderstanding is just one of several critical IT myths that could put your business at risk. Being small doesn't make you invisible; it often just means you're an easier entry point for attackers who are simply playing a numbers game. To see what other common misconceptions might be leaving you vulnerable, check out our guide on the top IT myths that could put your business at risk.
The first step toward real protection is accepting that every business, regardless of size, is on their radar.
How Your Industry Creates Unique Cyber Risks

A generic firewall can't protect you from threats it wasn't built to see. That’s the core truth most national IT providers miss when they look at a business in Salinas. They see "small business," but they fail to see the specific, on-the-ground ways you operate—and that oversight creates dangerous blind spots.
Your industry isn't just a label; it's a blueprint for your biggest cyber risks. The way you process payments, manage inventory, or even water your fields dictates exactly where a cybercriminal will strike. A defense strategy built for a generic office park in another state is guaranteed to fail you here in Monterey County.
It's time to move beyond generalized advice and connect cybersecurity directly to how you actually do business every single day.
For Agriculture: The Silent Threat in the Fields
Our region is the Salad Bowl of the World for a reason, and that deep reliance on agriculture creates a very specific set of vulnerabilities. Many farm operations across the Salinas Valley depend on legacy systems—older, on-premise technology that controls critical functions like irrigation, temperature monitoring, and processing equipment.
These systems are often reliable workhorses, but they were never designed with modern cybersecurity in mind.
What does this mean for you?
- On-Premise Vulnerabilities: Legacy control systems are rarely updated and often lack the security features of modern cloud-based tech. This makes them a prime target for ransomware attacks that can lock you out of your own equipment during a critical harvest.
- Unsecured IoT Devices: As farms adopt more "smart" technology like soil sensors and automated equipment, each new device creates a potential entry point for an attacker if not properly secured and monitored.
- Supply Chain Disruption: An attack doesn't just halt your operations; it can disrupt the entire supply chain that depends on your output, creating massive downstream consequences.
Imagine a hacker disabling your irrigation system during a heatwave or shutting down your cooling facility filled with perishable produce. This isn't science fiction; it’s a tangible risk that a standard "office" security plan completely overlooks.
For Hospitality: The High Stakes of Guest Data
For hospitality businesses in tourism hubs like Monterey and Pacific Grove, your biggest asset—and biggest risk—is guest data. You handle a constant firehose of personal information and credit card details, making you an incredibly valuable target for data thieves.
Your vulnerabilities often lie in the very tools you use to create a great guest experience.
Our research shows that many providers fail to address local industry-specific threats, outdated technology habits, or compliance issues relevant to Salinas-area businesses. They might install a firewall but fail to audit the security of the third-party booking platform where your guest data actually lives.
Common weak points we see in hospitality include:
- Vulnerable Booking Platforms: Third-party reservation systems can have security gaps that expose sensitive guest information, leaving you liable for a breach you didn't directly cause.
- Unsecured Wi-Fi Networks: Public-facing guest Wi-Fi, if not properly segmented from your main operational network, can provide a backdoor for criminals to access your point-of-sale systems and internal files.
- High Employee Turnover: The seasonal nature of hospitality often leads to inconsistent security training and credentials that aren't revoked when an employee leaves, creating orphan accounts that can be easily exploited.
Tailored Defense Is the Only Defense
These examples make it clear why a one-size-fits-all approach is doomed to fail. Protecting a farm's legacy irrigation controller requires a completely different strategy than securing a hotel's guest database. Generic vendors sell you a box; a true security partner analyzes your workflow first.
If you're a Salinas-area contractor, farm operation, or school struggling to make sense of all this, we’ll translate the tech into clear steps—tailored to your business, not just the industry standard. At Adaptive, we tailor our network security services to how Salinas and Monterey industries actually work, addressing threats like legacy systems, on-prem vulnerabilities, and cyber insurance readiness that others miss. Your business is unique. Your defense must be, too.
The Real Reason Your Employees Are a Security Risk

You’ve heard it a thousand times: human error is your biggest security problem. But if your fix is a once-a-year training video and a few reminder emails, you're missing the point entirely. The real vulnerability isn't just a simple knowledge gap; it's a deep misunderstanding of the threats your team faces right now.
Today's cyberattacks aren’t the clumsy, typo-filled emails from a Nigerian prince anymore. Criminals are now using AI to craft hyper-realistic phishing scams that can fool even your sharpest employees. These messages perfectly mimic your vendors, your bank, or even your own CEO, using language and context that feel completely legitimate.
A quick training session simply can't prepare someone for the psychological manipulation baked into these attacks. The real risk is the absence of a strong security culture—one built on continuous, real-world practice that builds defensive muscle memory.
Beyond Knowledge to Culture
A security-aware culture isn’t built with checklists; it’s forged through consistent practice and having dead-simple protocols to follow. It’s about shifting the mindset from "that's IT's job" to "this is everyone's responsibility." When your team feels empowered to question a suspicious request, they stop being a liability and become your strongest line of defense.
This kind of cultural shift hinges on a few key things:
- Making it Safe to Speak Up: Employees absolutely must feel comfortable reporting a potential mistake without fearing blame. A culture of punishment just encourages people to hide errors, which allows threats to spread silently through your network.
- Clear, Simple Protocols: When an employee spots something that feels off, what is the exact next step? A simple, documented process removes panic and guesswork. Our IT security policy template is a fantastic starting point.
- Leadership Buy-In: Security starts at the top. When leadership actively participates in security practices, the entire team takes it seriously.
The attacks targeting Salinas businesses are more sophisticated than ever. Ransomware and phishing are decimating SMBs, with a 20% year-over-year surge in attacks targeting them as 'soft targets.' Many are completely unprepared; 51% pay the ransom because their backups failed, costing an average of $84,000 per incident. Business email compromise (BEC) schemes are even more focused, with 85% targeting SMBs and contributing to $2.77 billion in global losses, as detailed in these small business cybersecurity statistics.
Transforming Your Team into a Human Firewall
So, how do you build this resilient culture? You move beyond boring, passive learning and into active defense. At Adaptive, we turn theory into practice with engaging, real-world drills that simulate the attacks your team will actually face.
The numbers are stark: 47% of SMBs were hit by ransomware in the past year, yet only 42% provide regular employee training. This is the gap where businesses fail. Believing you are "too small" to be a target is a risk you can no longer afford.
We help bridge this gap with tailored strategies that work for businesses right here in Monterey County.
- AI-Based Monitoring: We don't just wait for an employee to click a bad link. Our systems use advanced AI to detect and neutralize threats before they ever reach an inbox, cutting down the chance for human error from the very start.
- Real-World Phishing Drills: We run simulated phishing campaigns that mimic the latest attack trends. This isn't a "gotcha" exercise; it's a safe way for your team to learn what modern threats look like and practice the correct response without any real risk.
- Immediate, Actionable Feedback: When someone clicks on a simulated threat, they get instant, constructive feedback explaining the red flags they missed. This reinforces learning at the most critical moment—right when the mistake is made.
By implementing these proven solutions, you move from a passive, hope-based defense to an active, resilient one. You not only slash the risk of costly downtime but also start building the documented security posture needed to meet the strict cyber insurance requirements that generic vendors often overlook.
Navigating the Cyber Insurance Maze
Cyber insurance feels like a necessary safety net these days, but what happens when that net has giant, invisible holes in it? For a lot of Salinas businesses, that’s exactly the situation they find themselves in after an attack. They discover—at the absolute worst moment—that their expensive policy won’t pay out.
Why? It almost always comes down to failing to meet the strict, technical requirements buried deep in the policy's fine print. Insurers aren't just selling you a promise anymore; they're demanding proof that you're actively managing your cyber risk. Without that proof, your policy is little more than an expensive piece of paper.
Think of it this way: you wouldn't expect your home insurance to cover a fire if you’d yanked out all the smoke detectors and started storing gasoline next to the furnace. Cyber insurance carriers see a lack of security controls in the exact same way—as willful negligence that voids your coverage on the spot.
What Insurers Actually Demand From You
The days of getting a policy just by filling out a simple questionnaire are long gone. Today, insurers have a non-negotiable checklist of security controls you must have in place, running, and documented at all times. Failing to meet even one of these requirements can be grounds for denying your claim entirely.
Here are the absolute must-haves that insurers are looking for right now:
- Multi-Factor Authentication (MFA): This is the big one. You must have MFA enabled on all critical systems, especially email, remote access tools, and administrative accounts. No exceptions.
- Endpoint Detection and Response (EDR): Your old antivirus software just doesn't cut it anymore. Insurers require modern EDR solutions that can actively hunt for and neutralize advanced threats on your computers and servers.
- Regular Security Audits and Vulnerability Scanning: You need to prove that you are regularly looking for weaknesses in your own systems. This means having documented proof of routine scans and a real plan for fixing the issues you find.
- Tested Backup and Recovery Systems: Just having backups isn't enough. You have to prove you test your ability to restore from those backups regularly. If you can't show a recent, successful test, your claim could be in serious jeopardy.
- A Documented Incident Response Plan: When an attack happens, what's your step-by-step plan? Insurers want to see a formal, written plan that details exactly who to call and what actions to take.
Turning Your Policy into a Reliable Asset
This checklist can feel pretty overwhelming, but you don't have to tackle it alone. This is precisely where a proactive IT partner becomes essential. We don't just help you get insured; we help you stay insurable. Our job is to implement these required controls and, just as importantly, provide you with the ongoing documentation to prove it.
With a proactive partner, cyber insurance shifts from being a source of anxiety to a reliable asset. You gain the confidence that if the worst happens, you have the technical foundation and the paperwork to back up your claim.
We help Salinas-area businesses translate the complex demands of insurers into a clear, manageable action plan. We make sure your MFA is correctly deployed, your backups are tested, and your security posture is documented. Starting this process with a structured evaluation is key, and you can get a head start by using a proven cybersecurity risk assessment template to see where you stand.
By working with a local expert who understands both the technology and the insurance landscape, you move from passive defense to proactive resilience. You not only slash your risk of downtime but also ensure that your cyber insurance policy will actually be there to protect you when you need it most.
Your Proactive Cybersecurity Action Plan
Knowing the risks is one thing; doing something about them is what really matters. For Salinas business owners, this is the final, most critical step: turning awareness into a concrete plan that builds genuine cyber resilience. A proactive strategy isn't about buying more software—it's about creating a clear roadmap that minimizes risk, guarantees you can stay open for business, and transforms cybersecurity from a nagging expense into a powerful asset.
Let’s be blunt: a generic, one-size-fits-all approach is a failed approach. The truth is, your action plan has to be built around your specific operations. Whether you're running a farm, a school, or a hotel here in Monterey County, your defenses must be tailored to your unique challenges.
From Passive Defense to Proactive Resilience
The goal is to stop reacting to threats and start actively preventing them. This whole mindset shift rests on three pillars: a customized risk assessment, modern threat monitoring, and an incident response plan you've actually tested. When you focus on these areas, you build a security posture that not only protects your data but also keeps your cyber insurance carrier happy.
With Adaptive’s localized, tested solutions, SMBs move from passive defense to proactive resilience—reducing downtime risk and meeting cyber insurance requirements that generic vendors overlook. You can get a head start by checking out our Monterey Bay SMB cybersecurity prep list for 2026.
A proactive strategy doesn't just defend against today's attacks; it prepares you for tomorrow's. It's the difference between patching holes after a flood and building a stronger foundation before the storm even hits.
The process below breaks down the key steps to make sure your cyber insurance policy is an asset you can actually count on when you need it most.
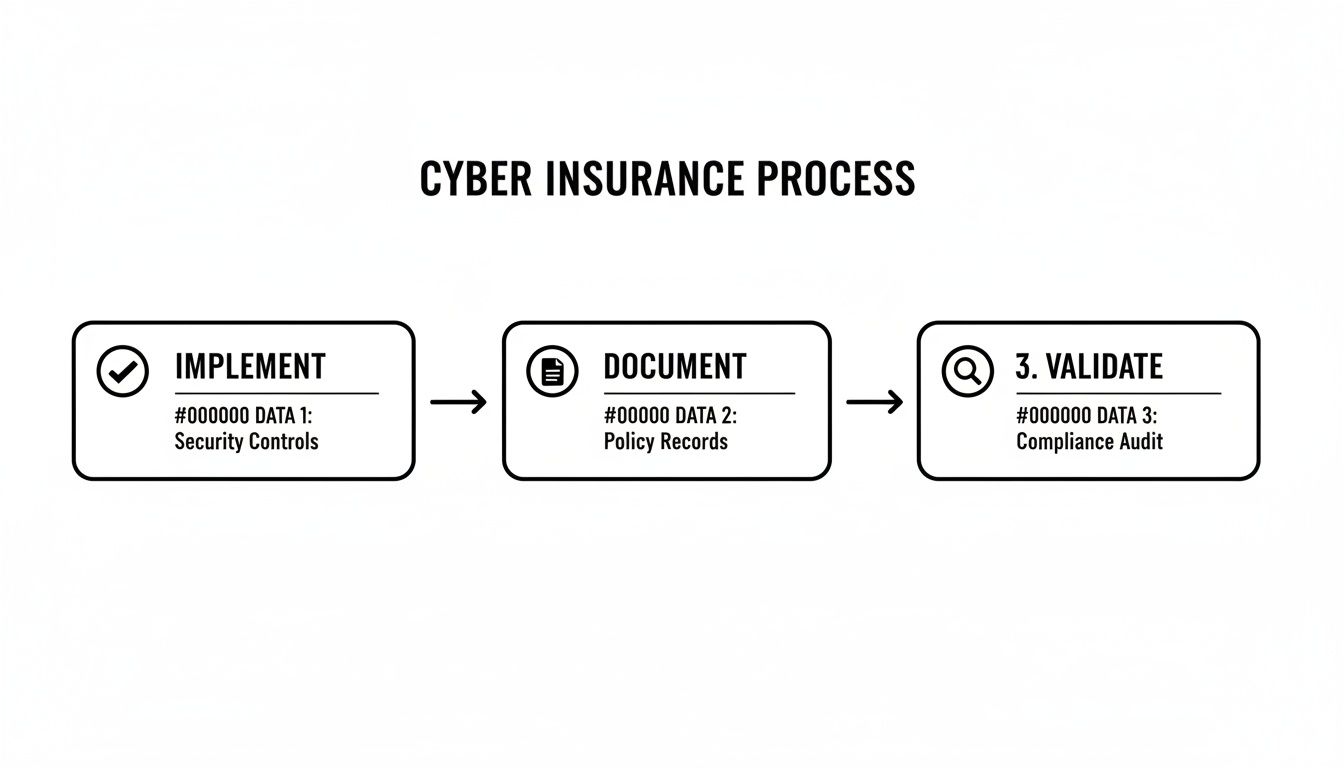
This simple three-step cycle—Implement, Document, and Validate—is the secret to turning that policy into a functional safety net. It’s what separates a piece of paper from real protection.
The path from basic protection to true cyber resilience can feel overwhelming, but it doesn't have to be. This simple roadmap prioritizes the steps every Salinas SMB should take to build a solid defense.
Your Proactive Cybersecurity Roadmap
| Priority Level | Action Step | Why It's Critical for Your Business |
|---|---|---|
| High | Multi-Factor Authentication (MFA) | This is your single most effective defense against stolen passwords. It stops 99.9% of automated attacks in their tracks. |
| High | Endpoint Detection & Response (EDR) | Traditional antivirus is no longer enough. EDR actively hunts for and neutralizes threats like ransomware before they can lock your files. |
| High | Regular Employee Training | Your team is your first line of defense. Simple, ongoing training on spotting phishing emails can prevent the majority of breaches. |
| Medium | Validated Backup & Recovery Plan | A backup you haven't tested is just a guess. Regularly validating your backups ensures you can actually recover your data after an incident. |
| Medium | Incident Response Plan (IRP) | When an attack happens, you need a clear playbook. An IRP tells everyone what to do, minimizing chaos, downtime, and financial loss. |
| Low | Vulnerability Management | This involves proactively scanning your systems for known weaknesses and patching them before attackers can find them. |
If you're a Salinas-area contractor, farm operation, or school struggling to make sense of all this, we’re here to help translate the technical jargon into clear, straightforward steps. Our entire focus is on creating a plan that’s built for your business—not some generic template. It’s time to build a defense that actually works for you.
We Get Asked This a Lot: Cybersecurity Questions from Salinas Business Owners
When we sit down with business owners in Salinas and Monterey, the same questions and concerns almost always come up. Let's cut through the jargon and get straight to the honest answers you need to make smart decisions for your company.
Is My Business Really a Target for Hackers?
Yes, absolutely. And thinking you're "too small to matter" is probably the single most dangerous assumption a business owner can make.
Hackers aren't manually searching for big company names; they're using automated software that constantly scans the internet for the easiest targets. A local Marina construction firm or a Pacific Grove retail shop with an unpatched server is often a much juicier, lower-effort payday than a huge corporation with a full-time security army.
They aren't looking for the biggest prize—they're looking for the easiest catch. Your size doesn't make you invisible; it makes you a low-risk, high-reward target.
What's the Single Biggest Security Mistake We Could Be Making?
Relying on a basic firewall and off-the-shelf antivirus software and calling it a day. While those tools are absolutely essential, they are just the starting line for security in 2024. They do very little to protect you from modern, sophisticated attacks.
Think about the real threats today: AI-powered phishing emails that perfectly mimic a vendor's invoice, tricking your accounts payable team into wiring money. Or ransomware that slips past old antivirus definitions by exploiting a software vulnerability you didn't even know you had.
The truth about SMB cybersecurity is that a passive defense is a failing defense. Real security requires a proactive, hands-on approach that includes ongoing employee training, modern threat monitoring, and a response plan you've actually tested before you need it.
How Much Should a Salinas Business Budget for Cybersecurity?
There's no magic number, as it really depends on your industry, your size, and the kind of data you handle. But the best way to frame it is to stop thinking of cybersecurity as an IT "expense" and start treating it like a core operational cost, just like your rent or business insurance.
Instead of asking, "How much does it cost?" the more important question is, "What is the cost of being shut down for a week?"
For a little perspective, recovering from a single ransomware attack can easily cost a small business tens of thousands of dollars in downtime, lost orders, and recovery fees. A proactive, managed security plan from a local provider like Adaptive Information Systems gives you enterprise-level protection for a predictable, affordable monthly cost. It’s simply a much smarter investment. We build our solutions around the financial realities of Salinas businesses, ensuring you get the protection you need without breaking the bank.
Ready to move from passive defense to proactive resilience? The team at Adaptive Information Systems can translate complex security needs into a clear, affordable action plan tailored for your Monterey County business.
Adaptive Information Systems
380 Main St, Salinas CA 93901 | 831-644-0300 | hello@adaptiveis.net
