At its core, a cybersecurity risk assessment template is a reusable, foundational document that guides your organization in systematically identifying, analyzing, and ultimately managing cyber risks. Think of it as a standardized framework that ensures a consistent and efficient approach to protecting your most critical digital assets.
Why a Standardized Template Is a Business Asset
Moving beyond scattered spreadsheets and inconsistent, ad-hoc checklists is a major step in maturing your security program. A well-designed risk assessment template isn’t just another document; it’s a powerful business tool that creates a universal language for risk across your entire organization. That consistency is its greatest strength.
When everyone from the IT helpdesk to the C-suite uses the same terms and methodology to talk about threats, communication suddenly becomes much clearer. Technical jargon gets translated into tangible business impact, finally bridging the gap between your security analysts and executive decision-makers. This unified view leads to smarter, data-driven security investments that actually align with your business goals.
Unlocking Efficiency and Strategic Focus
A solid template also frees up your most valuable security talent from getting bogged down in repetitive administrative work. Instead of building every assessment from scratch, your team can hit the ground running. This lets them focus their expertise on what truly matters: high-value threat analysis and proactive defense strategies.
This isn't a small gain. It means your team spends more time on:
- Deep-Dive Analysis: Investigating the "why" behind vulnerabilities, not just making a list.
- Proactive Threat Hunting: Actively searching for emerging threats before they can cause an incident.
- Strategic Planning: Aligning security controls with your long-term business objectives.
A robust template operationalizes your risk management strategy. It turns a theoretical exercise into a repeatable, measurable, and scalable business process, embedding best practices directly into your workflow.
Meeting Compliance and Building Trust
Standardization is also essential for meeting regulatory compliance. Frameworks and directives increasingly demand that you can demonstrate a consistent risk management process. For example, regulations like the EU’s NIS2 Directive require businesses to prove they have proportional cybersecurity measures in place. A good template is a foundational tool for doing just that—systematically identifying and treating risks to critical assets in a repeatable way that satisfies auditors.
This structured approach doesn't just prepare you for audits; it builds trust with clients, partners, and customers by showing a serious commitment to protecting their data. Whether you're a small local business or a growing firm, managing your security posture is critical. For organizations in specific regions, partnering with local experts provides a huge advantage. Our guide on managed cybersecurity in Salinas offers insights for businesses here in the Monterey Bay Area. This kind of diligent risk management, powered by a solid template, becomes a real competitive differentiator.
Choosing the Right Assessment Template for Your Needs
When it comes to cybersecurity risk assessments, one size definitely does not fit all. The template you choose has to match your organization's security maturity, the resources you have on hand, and what you’re ultimately trying to accomplish. If you pick the wrong one, you’ll either end up with a process that's too simple to be useful or one so complex your team never finishes it.
Your decision really boils down to three main flavors: qualitative, quantitative, and a hybrid of the two. Understanding how they differ is the first step toward building a risk management process that actually works for you and your team.
Qualitative vs. Quantitative Templates
For most organizations just dipping their toes into formal risk management, a qualitative template is the best place to start. This approach uses simple, descriptive scales—think low, medium, and high—to rate the likelihood and impact of a potential threat. It’s fantastic for getting a high-level, big-picture view of your risk landscape that’s easy to explain to executives and other non-technical folks.
For instance, a qualitative assessment might flag "unauthorized access to customer database" as a risk with a high impact and a medium likelihood. The idea isn't to pin an exact dollar amount on the problem but to prioritize your biggest worries based on their general severity.
On the other side of the coin, a quantitative template is built for more mature organizations. These businesses usually have the historical data and in-house expertise needed to run the numbers. This method assigns hard financial values to risks and their potential fallout. You might calculate the Annual Loss Expectancy (ALE) for a data breach, which turns an abstract cyber threat into a concrete financial figure that really grabs the attention of the C-suite and helps justify your budget requests.
Expert Insight: Honestly, for most small to mid-sized businesses, a qualitative or hybrid approach is far more practical. Jumping straight into a purely quantitative assessment can be incredibly resource-intensive and often leads to "analysis paralysis" if you don't have solid historical data to back up your calculations.
To help you decide which approach is the right fit, here’s a quick comparison of the two main template types.
Qualitative vs. Quantitative Risk Assessment Templates
This table breaks down the key differences to help you decide which template type best fits your organization's goals and capabilities.
| Attribute | Qualitative Template | Quantitative Template |
|---|---|---|
| Methodology | Uses descriptive scales (e.g., Low, Medium, High). | Uses numerical and financial data (e.g., dollar values, probabilities). |
| Best For | Organizations new to risk management; creating high-level overviews. | Mature organizations with access to historical data and statistical expertise. |
| Output | A prioritized list of risks based on severity rankings. | Specific financial figures like Single Loss Expectancy (SLE) and Annual Loss Expectancy (ALE). |
| Complexity | Relatively simple and quick to implement. | Complex and resource-intensive; requires specialized skills. |
| Communication | Easy to communicate to non-technical stakeholders. | Highly effective for executive and board-level financial discussions. |
Ultimately, the goal is to choose the template that provides actionable insights without overwhelming your team.
Aligning Your Template with Established Frameworks
To give your assessment real teeth and credibility, it’s a smart move to align your template with a well-known cybersecurity framework. These frameworks offer a proven, structured methodology for identifying and managing risk that stands up to scrutiny from auditors, regulators, and partners.
Two of the most respected frameworks are:
- NIST Cybersecurity Framework (CSF): A favorite in the U.S., the NIST CSF organizes everything around five core functions: Identify, Protect, Detect, Respond, and Recover. Building your template around NIST gives you a comprehensive and logical structure that everyone recognizes.
- ISO/IEC 27005: This is the international standard for information security risk management. It plugs directly into the widely adopted ISO 27001 certification, making it a perfect choice for global companies or any business pursuing ISO compliance.
Of course, there are many other templates out there, including hybrid models that blend qualitative and quantitative methods to give you a more rounded view. These become especially useful in complex areas like Vendor Risk Management (VRM), where you might be tracking the security posture of hundreds of third-party suppliers. For a deeper dive on these variations, the security experts at BitSight.com offer some great insights.
Building Your Cybersecurity Risk Assessment Template
Alright, let's get practical. Moving from theory to action is where your security posture really starts to take shape. Building a solid cybersecurity risk assessment template isn't about one giant task; it's about creating a reusable toolkit that's perfectly suited to your organization's unique environment.
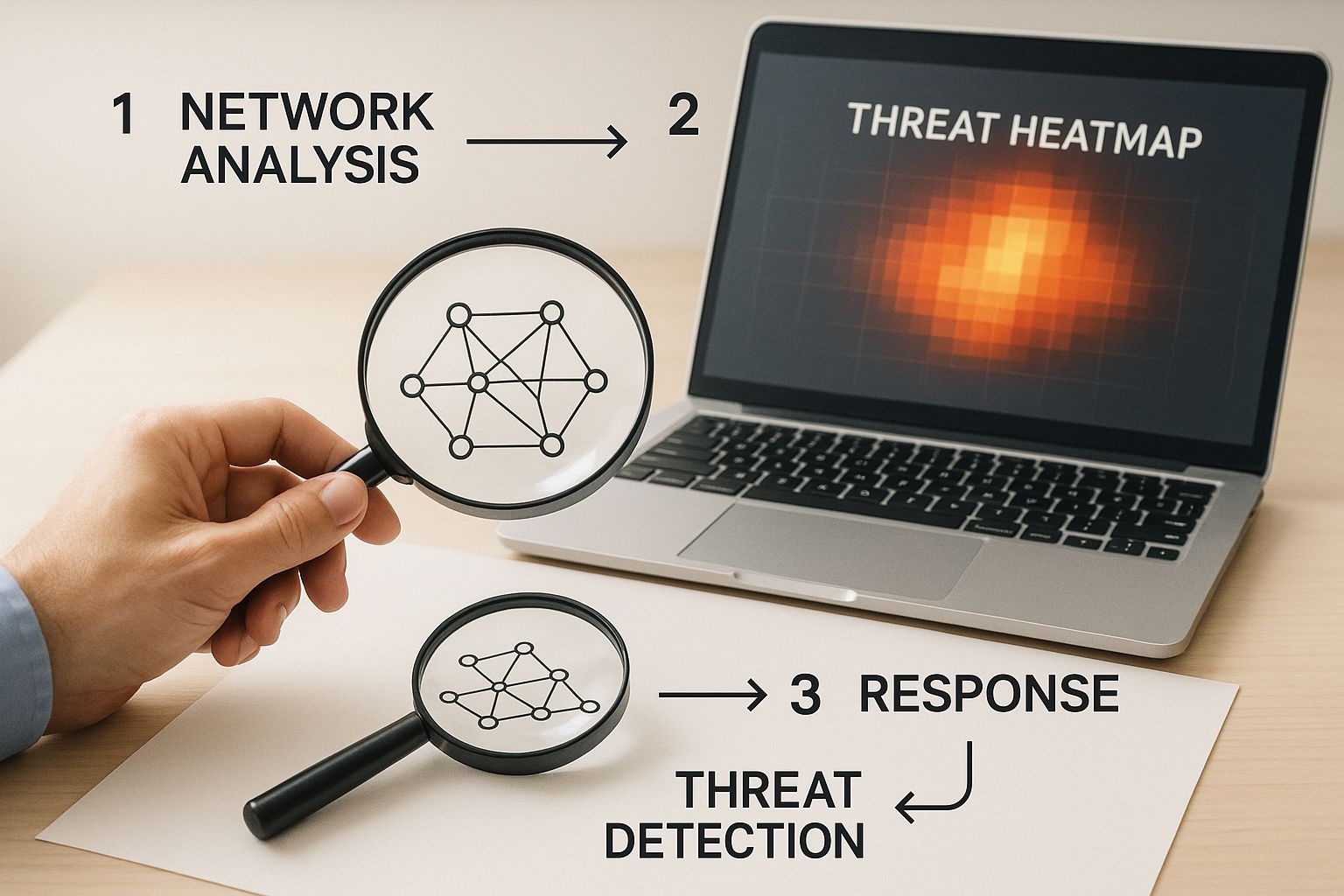
Think of it as a continuous cycle. Each part of the assessment informs the next, creating a loop that sharpens your understanding of risk over time.
As you can see, the process flows from identifying what you have, to figuring out how it can be attacked, and finally, to deciding what you’re going to do about it. Let’s break down these core pieces so you can build your own template from the ground up.
Asset Identification: You Can't Protect What You Don't Know
The absolute foundation of any good risk assessment is knowing exactly what you need to protect. This goes way beyond just a list of servers and laptops. A truly effective asset inventory is a detailed catalog of everything that holds value for your business.
Your template needs columns to track things like:
- Hardware Assets: Servers, workstations, mobile devices, firewalls, switches—if it has a power cord or a battery, it belongs here.
- Software Assets: Think applications, operating systems, and databases, paying special attention to the ones that run critical business functions.
- Data Assets: This is the big one. You have to identify and classify your sensitive information—customer PII, financial records, intellectual property, you name it.
- People: Yes, people are assets too! Key personnel with specialized knowledge or high-level access are critical components of your security landscape.
For every single asset, your template should note its owner, location, and a clear description of its role in the business. This context is absolutely vital for the next phase.
Threat and Vulnerability Identification
Once you know your assets, you can start thinking like an attacker. What could go wrong? This step is all about brainstorming how those valuable assets might be compromised. A threat is any potential cause of an incident, while a vulnerability is a weakness that a threat could exploit.
It's a simple but powerful distinction. A phishing email is a threat. An employee who hasn't had security awareness training is a vulnerability. One enables the other.
It's easy to focus on hackers from afar, but don't forget to look inward. A shocking 63% of cyber incidents have an internal component, whether it's malicious or just accidental. Your template has to account for risks from a disgruntled employee just as much as it does for a sophisticated external attack.
Risk Analysis: Putting a Score on It
This is where you connect the dots between threats, vulnerabilities, and actual business impact. Here, you'll assign scores for likelihood (How likely is this to happen?) and impact (How bad would it be if it did?). Honestly, a simple 1-5 or a Low-Medium-High scale usually works best. Don't overcomplicate it.
For example, a ransomware attack hitting your primary file server might have a "Medium" likelihood but a "Very High" impact. Your template should be set up to automatically calculate a final risk score (often by multiplying the two values), which lets you create a prioritized list of what to tackle first.
Risk Treatment and Mitigation Controls
The last part of your template is the most important: the action plan. For every risk you've identified and scored, you need to document how you plan to handle it. This section outlines the specific security controls you'll put in place to bring that risk down to an acceptable level.
Your template absolutely must include fields for:
- Mitigation Control: The specific action, like "Implement multi-factor authentication for all remote access."
- Owner: The person or team on the hook for getting it done.
- Deadline: A realistic timeline for completion. Accountability matters.
- Status: A simple way to track progress (e.g., Not Started, In Progress, Complete).
This final component is what transforms your template from a static document into a living, breathing management tool that drives real security improvements.
How a Template Drives Real-World Business Value
It’s easy to think of a cybersecurity risk assessment template as just another document—a box to check. But in reality, it’s a strategic asset that delivers tangible, real-world returns. Its biggest benefit? It makes high-level cybersecurity accessible, especially for organizations that don’t have a massive, dedicated security team on standby.
By standardizing the process, you create a reliable, repeatable method for evaluating your security posture. This isn't just about efficiency; it's about consistency. When every assessment follows the same framework, you drastically reduce the chance of overlooking critical vulnerabilities. It also gives you a clear, comparable history of your risk profile over time, which is invaluable for spotting trends and preventing costly breaches.
Powering Strategic Business Decisions
The true power of a good template shines when you move beyond routine internal audits. It quickly becomes an essential tool for navigating major business decisions where risk evaluation is non-negotiable.
- Mergers and Acquisitions: Think you're just buying a company? You could be inheriting its security nightmares, too. A standardized template lets you assess a target company's security using the exact same yardstick you use for your own business, preventing nasty surprises down the road.
- Vendor Risk Management (VRM): In today's interconnected world, your vendors' security weaknesses can easily become your own. A template gives you a systematic way to evaluate every single third-party partner, whether it's a software provider or a critical supplier.
- Market Expansion: Launching a new product or moving into a new region always introduces new risks. Your template provides a ready-made framework to proactively identify and tackle these challenges before they can derail your launch.
Adopting this kind of repeatable process has proven economic benefits for businesses of all sizes. For small and medium-sized businesses (SMBs) that often lack a dedicated security department, a template is a game-changer. It provides a structured way to identify assets and threats without getting bogged down in endless manual work. This ensures nothing critical gets missed, reducing the likelihood of expensive data breaches.
For local businesses, understanding the regional threat landscape is a key piece of the puzzle. That’s why we created a specific guide on cybersecurity in Salinas. You can also find more insights on how a downloadable risk assessment template can streamline planning and deliver measurable improvements on memcyco.com.
A strong template transforms risk assessment from a reactive compliance chore into a proactive, strategic business function. It provides the data-driven clarity needed to align security investments with organizational goals, protecting your bottom line and your reputation.
By making the assessment process uniform, the template also helps build a consistent risk-aware culture across your entire organization. It guarantees that assessments conducted in different departments or locations all adhere to the same high standards. This gives leadership a clear, unified view of the company's overall security health—something you just can't get with an ad-hoc approach.
Common Mistakes to Avoid When Using Your Template
Rolling out a cybersecurity risk assessment template is a huge step in the right direction. But even the sharpest tools can be misused. I've seen a few common pitfalls quietly sabotage a company's hard work, turning a proactive security strategy into little more than a box-checking exercise.
The biggest trap? Treating the risk assessment as a one-and-done project. You fill out the template, show everyone the findings, and then it gets buried in a folder until next year’s audit. That "set it and forget it" mindset is a recipe for disaster, because the threats targeting your business are changing by the minute.
An effective risk assessment isn’t a snapshot; it's a motion picture. It has to be a living, breathing process that adapts as you adopt new tech, as new threats pop up, and as your own business evolves.
Falling into the Silo Trap
Another major mistake is letting the IT team handle the assessment all by themselves. Sure, your tech folks have critical knowledge, but they can't see the whole picture from their corner of the office. Risk is a business-wide problem, not just an IT one. When other departments are left out of the conversation, you miss out on absolutely essential context.
For a truly complete view, you have to bring a diverse group to the table:
- Finance: These are the people who can put a real dollar amount on what downtime or a data breach would cost.
- Operations: They know the critical day-to-day processes that actually keep the lights on and the business running.
- HR: They have the inside track on insider risks and can spot gaps in security awareness training.
- Legal: This team can flag the serious compliance and regulatory headaches you might face.
Working in an IT bubble just gives you a narrow, tech-focused report that completely misses the true business impact of cyber risks.
Overlooking the Human Element
It's so easy to get hyper-focused on firewalls, servers, and software bugs. Those things are definitely important, but this approach often ignores the biggest security variable of all: your people. By some estimates, a staggering 63% of security incidents involve someone on the inside, whether their actions were malicious or just an honest mistake.
Your risk assessment has to account for these human-related risks. I'm talking about everything from weak security training that leaves employees vulnerable to phishing emails, to the possibility of a disgruntled employee deciding to misuse their access. To cover all your bases, you need a strategy that includes both technical and human-centric defenses, which is a key part of any good small business guide to network security.
Using Generic Risk Descriptions
Finally, a template filled with vague, generic descriptions is pretty much useless. What does a risk like “Poor access control” even mean? It doesn't point to a clear solution, so you can't take action on it. You have to get specific.
Instead of that generic statement, try something concrete. For example: “Marketing interns have inherited excessive read/write permissions to the primary customer database, creating a risk of accidental data modification or deletion.” See the difference? Now you know exactly what the problem is, who's involved, and what could go wrong. That makes it a whole lot easier to build a targeted plan to fix it.
Of course. Here is the rewritten section, crafted to sound completely human-written and aligned with the provided examples.
Answering Your Top Risk Assessment Questions
Even with a great cybersecurity risk assessment template in your hands, you’re bound to run into some practical questions. Getting these sorted out is key to making sure your risk management efforts are actually effective and not just a box-ticking exercise.
Let's dig into some of the most common questions we hear from organizations just like yours.
How Often Should We Conduct an Assessment?
This is easily one of the most frequent questions we get. The short answer? You should be doing a full, comprehensive risk assessment at least annually.
But that’s just the baseline. A much smarter approach is to treat risk assessment as a living process. This means you should kick one off whenever your business goes through a major change.
Think about triggers like:
- Rolling out a significant new piece of technology.
- Going through a merger or acquisition.
- Making a big pivot in your business model.
- Expanding your operations into a new region with different regulations.
For your most critical systems—the ones that would bring your business to a halt if they went down—you should probably be looking at them more often, maybe even quarterly. The idea is to keep your security in lockstep with your business, not to create a report that just gathers dust on a shelf.
What Is the Difference Between Risk and Vulnerability Assessments?
This one trips a lot of people up, but the distinction is crucial. A vulnerability assessment is a very technical, hands-on process. It’s all about running scans to find specific weak spots in your tech stack, like unpatched software, open ports, or sloppy cloud configurations. Its job is to give you a list of potential flaws.
A cybersecurity risk assessment, on the other hand, pulls the camera back for a much wider, more strategic view. It takes the raw data from those vulnerability scans and layers on critical business context.
A vulnerability scan tells you what's broken. A risk assessment helps you decide what to fix first based on the potential business impact. It answers the "so what?" question by looking at which threats could actually exploit a weakness and the real-world damage it would cause.
Can We Use a Generic Template or Do We Need a Custom One?
Starting with a generic, downloadable cybersecurity risk assessment template is a fantastic move, especially if your team is just getting started with formal risk management. It gives you a solid, proven structure and makes sure you don't miss any essential steps, from identifying assets to planning your response.
But here’s the thing: no off-the-shelf template will be a perfect fit for your business right away. Think of it as a starter kit, not a finished product.
The real value comes from customization. You absolutely have to tailor it to your world. That means adjusting the asset categories, tweaking the risk-scoring criteria, and selecting controls that make sense for your specific industry, regulatory pressures, and how you actually operate. A template is the blueprint; your customized version is the powerful tool that will truly protect your business.
Ready to build a resilient and secure IT environment for your business? Adaptive Information Systems provides expert IT consulting and managed services to help businesses in Salinas and the Monterey Bay Area thrive. Discover our solutions at https://adaptiveis.net.