In today's world, keeping your Salinas business safe means more than just locking the doors at night. You need a smart plan to protect your digital information. This guide will show you how key services like firewall management, real-time threat detection, and data encryption work together to shield your company from online threats. It’s about building a strong defense for your business right here in Monterey County.
Why Cyber Threats Are Targeting Salinas Businesses
If you own a small or mid-sized business here in Salinas, you might think you’re too small for cybercriminals to notice. Unfortunately, that's exactly what they hope you're thinking. Hackers are actively targeting local companies in Monterey County because they know you're busy running your business and might have limited IT resources. This makes businesses in key local industries, like agriculture and financial services, especially attractive targets.
This isn’t just a guess. According to our recent marketing insights, cybersecurity is the top concern for local business owners. Attackers aren’t just looking for a quick payout; they want your valuable data—customer lists, financial records, and business plans. A poorly managed network is like an open invitation for them to walk right in.
The Real-World Risks You Face
These threats aren't just stories you see on the news. They have real, often devastating, consequences for businesses from Carmel to Marina. Imagine an ag-tech company’s operations being shut down by ransomware during harvest season. Or a local hotel losing its reputation after a customer data breach.
The consequences of a weak network are serious:
- Data Breaches: Your private customer or company information gets stolen.
- Regulatory Fines: You could face heavy fines for not protecting data properly.
- Loss of Customer Trust: A damaged reputation can be almost impossible to fix.
The national data confirms what we're seeing locally. A shocking 43% of all cyberattacks target small businesses. On top of that, smaller companies were involved in 46% of all data breaches.
To help you see the risks more clearly, here are some of the most common attacks we see affecting businesses in our area.
Top Cyber Threats Facing Salinas SMBs
| Threat Type | What It Looks Like | Potential Business Impact |
|---|---|---|
| Phishing | An employee gets an email that looks real, asking them to click a link and enter a password. | Hackers can steal money, install viruses, or lock you out of your accounts. |
| Ransomware | All your business files are suddenly locked, and a hacker demands money to get them back. | Your business grinds to a halt. You can lose data, money, and customer trust. |
| Business Email Compromise (BEC) | A scammer pretends to be you and emails your accountant to wire money to a fake account. | You could lose thousands of dollars in a single transaction. |
| Malware | A computer slows down to a crawl, or you find out your private files are being sold online. | Your data is stolen, your network is compromised, and your systems are damaged. |
These examples show how vulnerable your business can be if your defenses aren't strong enough.
The Hidden Vulnerability: Human Error
Of course, technology is only one part of the solution. A simple mistake by an employee can cause a major security breach. Someone clicking on the wrong link in an email can let a hacker bypass even the best firewall.
This is why regular employee training is so important. Your team needs to know how to spot a scam. To learn more about this specific risk, check out our guide on the dangers of email phishing and how to spot the red flags.
Investing in reliable network security is no longer just an IT cost; it's a fundamental part of running a successful business. It's about protecting your profits, your reputation, and the trust you've worked so hard to earn in the Salinas community.
Decoding Your Network Security Toolkit
When you hear "network security," it’s easy to feel like you need to be a tech expert. Let's simplify it. What you really need are practical tools that protect your business every single day.
Think of it as layers of security, where each layer does a specific job. The goal is to help you understand what you're investing in and why each part is critical for your business. After all, network security threats are rising in California, and small to mid-sized businesses in Salinas are increasingly targeted due to weaker defenses and limited IT resources.
The Core Components of Your Defense
At the heart of any good security plan are a few key tools. These aren't just for big corporations anymore; they are affordable and absolutely necessary for any local business, whether you're a CPA in Monterey or a packing house in Marina.
Your security plan should include:
- Firewall Management: This is your digital security guard. A well-managed firewall watches all the traffic coming into and out of your network, blocking anything suspicious before it gets inside.
- Real-Time Threat Detection: This is like a 24/7 security camera system. It actively looks for strange activity on your network and stops threats as they happen—not after the damage is done.
- Endpoint Protection: This secures every device—laptops, desktops, and phones—that connects to your network, protecting you from threats no matter where your team is working.
- Data Encryption: This scrambles your sensitive data, making it unreadable to anyone without the key. It protects your information whether it’s stored on your server or being sent in an email.
A common mistake is thinking one tool is enough. Real security comes from having these parts work together. A strong firewall is great, but it can't stop a virus an employee accidentally downloads. That’s why endpoint protection and threat detection are so important.
If you're looking to build a stronger foundation of knowledge, this guide on network security fundamentals is a great place to start.
Making Enterprise-Level Tools Accessible
In the past, these kinds of powerful tools were too expensive for most small businesses. That has changed. At Adaptive Information Systems, our mission is to offer enterprise-level network security at small-business prices, making advanced protection accessible without blowing the budget.
This gives you a big opportunity. Your local competition often overlooks cybersecurity best practices. By taking security seriously, you can gain a reputation advantage and show customers you can be trusted. We’ve seen a growing interest in this; our recent Pro Max digital campaign received 139,000 impressions, highlighting the demand for IT solutions across the Salinas region.
A modern firewall is a powerful first line of defense. To learn more, check out our guide on choosing the best firewall for your small business. When you partner with a team like ours that provides ongoing threat monitoring and compliance support, your defenses stay up-to-date as new threats emerge.
How to Conduct a Practical Security Self-Assessment
Before you can protect your Salinas business, you need to know where your weak spots are. It’s tempting to jump right into buying new software, but first, take a moment to look at your current setup. A simple security check can reveal major risks you might not even know you have.
This isn't a deep technical dive. It's a practical way for you, the business owner, to get a quick snapshot of your defenses. Asking the right questions now helps you identify your biggest risks and prepares you to have a productive conversation with an IT partner. This way, you can focus on fixing the most important problems first.
Key Areas for Your Review
Let's start with the basics. From our experience, these are the areas where we find the most common—and most preventable—risks. A quick, honest review here can tell you a lot.
Go through these key parts of your business:
- Access Control: Who can see your most sensitive data, like financial records and customer lists? Is access limited only to employees who absolutely need it for their jobs?
- Password Policies: Be honest. Are your employees using simple passwords like "Salinas123"? Do you require strong, unique passwords for different systems? Are they changed regularly?
- Software Updates: When was the last time you made sure every computer and program is fully updated? Hackers love to sneak in through old, outdated software.
- Data Backups: Do you back up your important data regularly? And here's the real test: have you ever tried to restore from that backup to make sure it actually works?
Doing a basic check like this is the first step toward building a stronger defense. It turns the vague idea of a "cyberattack" into a clear to-do list, making the challenge of how to protect your Salinas business with reliable network security services much easier to handle.
Asking the Tough Questions
Okay, now let's dig a little deeper. Grab a notepad and be completely honest with your answers. The goal is to see your business the way a security expert—or a hacker—would.
A full self-audit can feel like a lot, but you don't have to start from scratch. For a more detailed guide, you can use our cybersecurity audit checklist for small businesses to walk you through a more complete review.
But to get started right now, ask yourself these questions:
- Employee Onboarding and Offboarding: What happens when an employee leaves your company? How quickly is their access to email, files, and other systems shut down? Old accounts are open doors for trouble.
- Physical Security: Who can physically walk into your server room or get to the computers with your most important data? Are these areas locked after hours? We often forget about simple physical security.
- Third-Party Vendors: Think about your accountant, marketing agency, or any other vendor you work with. Do they have access to your network? Are you sure their security is as strong as yours?
This self-assessment gives you a clear starting point. It helps you understand where your biggest risks are today so you can find the right solutions to protect what matters most.
Choosing the Right Security Partner in Monterey County
When it comes to IT, finding the right provider is about more than just technical skill. It's about finding a partner who understands our local economy. A generic company won't get the unique pressures a Salinas Valley farm faces during harvest or the security needs of a Pacific Grove hotel during tourist season.
You need a local partner.
This is where asking the right questions is key. You're not just buying a service—you're investing in a trusted relationship. The goal is to find a team that gives you enterprise-level protection that actually fits a small business budget.
What to Look for in a Local Partner
Let's be realistic: hiring a full-time, in-house cybersecurity expert is too expensive for most local businesses. That talent is in high demand, with an average salary in Salinas around $142,854 per year. That's a huge expense for one expert.
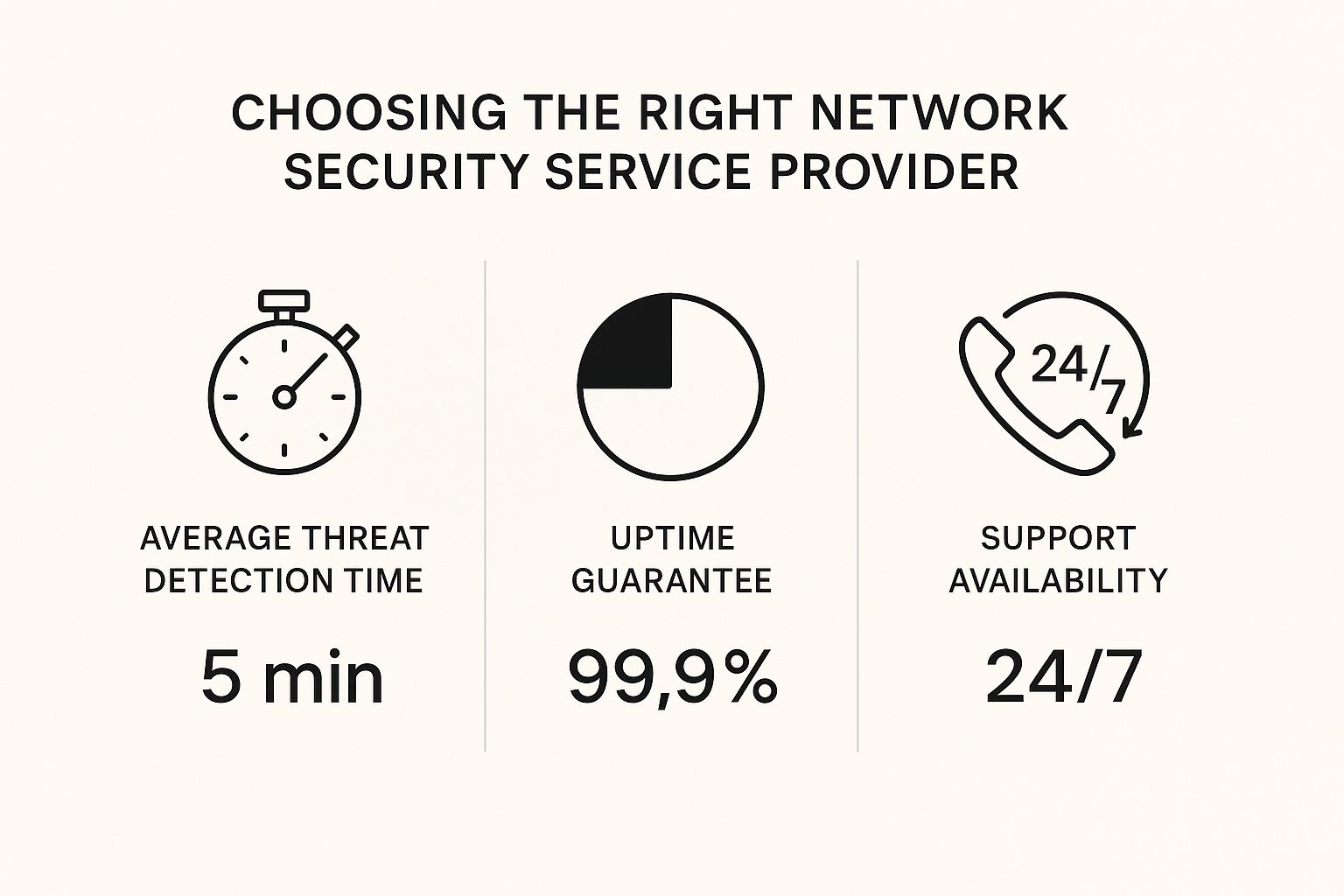
Instead, partnering with a managed security provider gives you an entire team of specialists for a fraction of that cost. When you're looking for a partner, there are a few key things you need to ask about.
These numbers aren't just for show. They can be the difference between a minor problem and a major crisis. This is the level of service you should expect.
Essential Questions to Ask Any Potential Vendor
Before you sign any contract, you need to get clear answers to a few critical questions. Their answers will tell you everything you need to know about their skills and their commitment to you.
- What is your average response time for a critical security alert? Anything more than a few minutes is too long. In a cyberattack, every second matters.
- How do you stay up-to-date with new threats and regulations? The world of cyber threats changes every day. You need a team that is always learning, not one that's playing catch-up.
- Can you provide local references or case studies? A provider with deep roots in Monterey County should be happy to share their success stories with businesses just like yours.
The right partner acts like an extension of your own team. They should be just as invested in your success as you are, providing the constant monitoring and support that keeps you protected.
Deciding between hiring in-house and working with a partner is a big decision. Here’s a quick comparison to help you weigh your options.
Comparing In-House IT vs. a Managed Security Partner
This breakdown can help you decide which approach is the best fit for your Salinas business.
| Factor | In-House IT Staff | Managed Security Partner (like Adaptive IS) |
|---|---|---|
| Cost | High fixed costs (salaries, benefits, training). | Predictable monthly fee. Access to top-tier tools at a shared cost. |
| Expertise | Limited to what 1-2 people know. | Access to a whole team of specialists in security, cloud, and compliance. |
| Availability | Limited to business hours, vacations, and sick days. | 24/7/365 monitoring and support. No gaps in protection. |
| Scalability | Slow and expensive to grow. Hiring takes time. | Easily scales with your business as your needs change. |
| Proactive Approach | Often busy fixing today's problems (reactive). | Focuses on preventing problems before they happen (proactive). |
While an in-house team is dedicated to you, a managed partner provides broader expertise and round-the-clock coverage that's hard for a small business to match on its own.
Finding the right partner is a crucial first step. For more help, check out our guide on how to choose from different types of IT service providers to see which model truly fits your needs. Your partner should make advanced protection a reality, not a budget-breaking luxury.
Building a Security-First Team Culture
Your technology is only half of your security plan. The best firewall in the world can't stop a well-meaning employee from clicking on a clever phishing link.
That’s why creating a security-first culture is one of the most powerful things you can do to protect your Salinas business. It’s not about blaming people for mistakes. It’s about giving your team the knowledge they need to become your best security asset.
When your staff knows what to look for, they become your first line of defense. This is critical, especially since cybersecurity remains the top concern for local business owners in our region's key industries, like agriculture and financial services.
From Awareness to Action
A security-conscious culture starts with simple, consistent training. This doesn't need to be complicated or expensive. The goal is to make good security habits a normal part of everyone's day.
To get started, focus on these key areas:
- Phishing Recognition: Hold short, regular training sessions showing real examples of scam emails. Teach your team to hover over links before clicking and to be suspicious of any email that creates a sense of urgency.
- Strong Password Habits: A weak password is like leaving your front door unlocked. Enforce a policy that requires long, unique passwords and encourage the use of a password manager. For more details, see our guide on password policy best practices.
- Reporting Suspicious Activity: Create a clear, no-blame way for employees to report anything that seems odd. An employee needs to feel safe saying, "I think I might have clicked on something bad," without fearing punishment. Reporting a problem quickly can make a huge difference.
Turning your team into security champions is about creating an environment where everyone understands they play a part. It's about shared responsibility. When security is part of your company culture, it becomes everyone’s job to protect the business.
Making Security an Ongoing Conversation
Security training can't be a one-time event. Online threats are always changing, so your team's awareness needs to keep up. Think of it less like a single class and more like an ongoing conversation.
A simple monthly security tip in a company newsletter or a quick five-minute update at a team meeting can keep these practices fresh in everyone's mind. This ongoing reinforcement keeps your "human firewall" strong, protecting your customer data and your Salinas business's reputation from the inside out.
Your Action Plan for a More Secure Business
Feeling overwhelmed by network security? Let’s make it simple. Protecting the Salinas business you've worked so hard to build starts with a clear, straightforward plan—one that tackles your real risks without breaking your budget.
Your strategy comes down to three things: understanding your weak spots, putting basic security tools in place, and turning your team into your best defense. Getting this wrong can be costly. Poorly managed networks can result in data breaches, regulatory fines, and loss of customer trust — consequences many local companies can’t recover from.
The first step is easy and comes with no strings attached.
Taking action isn't just about preventing a disaster; it's about building a stronger, more trustworthy business. When you show you're committed to security, you gain a powerful advantage in the local market.
As you think about your next move, it helps to know your options. To get a better sense of a complete strategy, this resource on essential security solutions for businesses is a great starting point.
Secure your Salinas business today — contact Adaptive Information Systems for a free network security consultation.
We Get These Questions All the Time
As a local IT partner, we've talked with countless business owners across Monterey County. Over the years, we've noticed the same questions come up again and again. Let's answer some of the most common ones we hear right here in Salinas.
"Isn't Professional Network Security Too Expensive for a Business My Size?"
This is probably the biggest myth we hear. Many owners think "enterprise-level security" means a price tag only huge companies can afford.
But the reality is, the cost of not having professional security is almost always higher. A single data breach can lead to huge recovery costs, fines, and a complete loss of your customers' trust. Most small businesses can't bounce back from that.
Modern managed services are designed to be affordable. We offer predictable, monthly plans that give you a full team of experts and advanced security tools—all for a fraction of the cost of hiring even one full-time IT person.
"My Business Is Small. Why Would a Hacker Even Bother With Me?"
This surprises a lot of people: hackers rarely pick their targets by hand. They use automated programs to scan the internet for any weak system, no matter how big or small the business is.
It's a numbers game. Hackers know that smaller businesses often have weaker defenses, which makes you an easy target for ransomware and data theft.
It’s not personal—it’s just business for them. To a hacker, your company is just another unlocked door to valuable data, and they're betting your door is unlocked.
Being proactive is the only way to prove them wrong and keep your business from becoming an easy target.
"How Long Does It Take to Get Proper Network Security in Place?"
Getting started is faster and easier than you might think. When you have an experienced partner handling it, basic protections like firewall management and endpoint security can often be set up in just a few days.
We manage the entire process for you, from the first assessment to the final setup. This means you can stay focused on running your business without getting stuck in the technical details. The whole point is to get your defenses up and running quickly to close any security gaps without causing a lot of disruption.
Adaptive Information Systems
380 Main St, Salinas CA 39301 | 831-644-0300 | hello@adaptiveis.net