Think of a cyber security risk assessment service as a health check-up for your company’s technology. Experts come in to find your most important digital files and systems, figure out the threats that could harm them, and find weak spots in your defenses. What you get is a clear, simple plan to protect your Salinas business from online dangers.

Why Your Salinas Business Needs a Digital Game Plan
As a business owner in Monterey County, you already know how to manage risk. If you run a farm in Salinas, a hotel in Monterey, or a shop in Carmel, you naturally protect your physical property—your equipment, your products, and your building. A cyber security risk assessment does the same thing for your digital world.
Here’s an easy way to think about it: a farmer would never plant crops for the season without checking the irrigation system for leaks. A restaurant owner wouldn't open for a busy weekend without making sure their payment system works. In the same way, you can’t afford to run your business without knowing where your digital "leaks" and weak spots are.
Moving Beyond Guesswork
Many local business owners think they're too small to be a target for cybercriminals. This is a dangerous myth. The truth is, attackers often go after small and mid-sized businesses because they assume security isn't a top priority. A professional assessment takes the guesswork out of your security plan.
Instead of worrying about vague threats, you get real answers to important questions, like:
- What is our most important data, and where is it stored?
- Do our employees know how to spot scams like phishing emails?
- Is all of our software up-to-date, or are there known security holes?
- What would happen to our business if our systems went down tomorrow?
A risk assessment is the foundation of any strong security plan. It’s not about buying every new security gadget. It's about making smart choices to protect what truly matters to your business. It's the first step from reacting to problems to preventing them.
A proper assessment gives you a clear roadmap. It helps you spend your IT budget where it will do the most good. You'll know exactly what to fix first, getting the most security for your money. This is the heart of our mission: offering enterprise-level IT at an affordable price for local SMBs. It’s a key part of the smart planning we discuss in our overview of business technology consulting.
What a Cyber Risk Assessment Actually Involves

So, what do cyber security risk assessment services actually do? Let’s make it simple. It's not about confusing you with tech talk. It’s a practical business process, just like the ones you use every day.
Think of it this way: if you own a popular restaurant in Pacific Grove, you check your kitchen equipment before every shift to prevent a breakdown. If you manage an ag business in the Salinas Valley, you walk the fields checking for problems before planting season.
A cyber risk assessment uses that same common-sense approach for your company's technology. It's a complete health check for your entire digital operation. The goal is to answer a few simple but very important questions about your business.
Identifying What Needs Protection
First, we need to figure out what's most valuable. We'll work with you to make a list of your important digital assets. This isn't just about computers. It's about the information that makes your business run.
Common digital assets for local businesses include:
- Customer Information: This could be a client list, contact details, or even sensitive financial data.
- Financial Records: This includes everything from payroll files and accounting records to online banking passwords.
- Business Systems: This covers your sales systems, online booking tools, or any special software you use every day.
By knowing exactly what you need to protect, you can focus your security efforts where they matter most. It's a key part of our cybersecurity risk assessment process.
Spotting Threats and Vulnerabilities
Once we know what’s important, the next step is to find out what could harm those assets. We look at this in two ways: threats (the "what") and vulnerabilities (the "how").
A threat is an outside danger, like a scam email trying to trick an employee or a ransomware attack that locks up your files. A vulnerability is an inside weakness a threat could use—like old software, a weak password rule, or a lack of security training for your team.
Think of it like securing a building. A burglar is the threat. An unlocked window is the vulnerability. You can't control the burglar, but you can definitely lock the window.
Prioritizing Risks and Creating a Plan
The final step puts it all together. We figure out how likely it is that a threat will use one of your weaknesses and what the damage would be to your business. To do this, many experts use a guide to the risk management matrix to help sort and prioritize issues.
This process helps you make smart decisions with your budget. For example, the risk of a main server crashing might be a much higher priority to fix than a small software bug on one computer.
This smart focus is why businesses are spending more on these services. The global cyber security market is expected to grow from USD 301.91 billion in 2025 to almost USD 878.48 billion by 2034. This shows just how important this planning has become.
At the end of the process, you get a clear, actionable plan—a roadmap to make your business safer without breaking the bank.
Our Step-by-Step Risk Assessment Process
So, how does a cyber security risk assessment service work for a local business like yours? We use a clear, simple process without the confusing tech talk. Our goal is to give you a practical roadmap you can actually use, not a thick report that sits on a shelf.
Our approach is built on a simple, three-step foundation. We want you to feel confident and informed at every stage, knowing what we’re doing and why it matters for your company’s safety.
This image shows our process: finding assets, analyzing weak spots, and planning fixes.
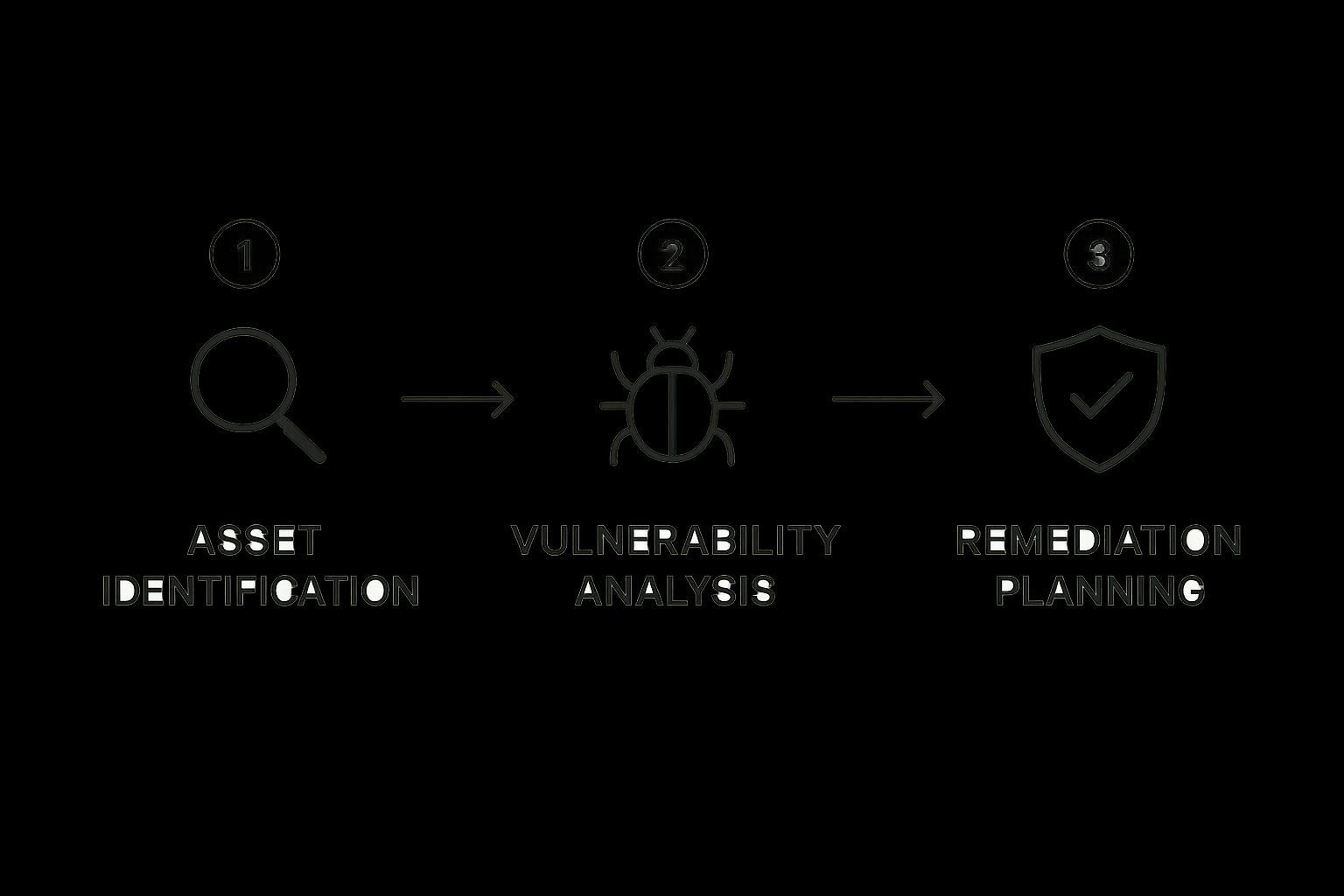
Each step builds on the one before it. This makes sure we create a security plan that’s right for your business needs and your budget.
The Three Phases of a Risk Assessment
To make it easy to understand, here is our process in a simple table. It shows you exactly what we do and why it's important for protecting your business.
| Phase | What We Do For You | Why It Matters for Your Business |
|---|---|---|
| 1. Identification | We list every important piece of technology and data your business uses, from servers to software. | You can't protect what you don't know you have. This makes sure nothing important is left exposed. |
| 2. Analysis | We find potential threats and the weak spots in your current setup that an attacker could use. | This step connects outside dangers (like ransomware) with inside weaknesses (like old software). |
| 3. Remediation | We create a priority list to fix the biggest issues first, balancing security with your budget. | You get a clear, practical plan for what to fix now, next, and later. This makes your security investment count. |
This organized approach ensures we cover all the bases. You're left with a real plan that delivers real security improvements.
Phase 1: Identification and Scoping
First, we need to understand your business. We can't protect what we don't know about, right? We’ll sit down with you to map out all of your critical digital assets—the technology and data that are essential for your daily operations.
For a Salinas accounting firm, this might be their client financial database and tax software. For a Monterey hotel, it could be their guest reservation system and online payment tool.
We create a detailed list of everything that matters, including:
- Hardware: Servers, computers, laptops, and network equipment.
- Software: Your main programs, from accounting software to customer management (CRM) tools.
- Data: Customer lists, employee records, financial info, and any unique business information.
This first phase gives us a complete picture of your digital footprint, so nothing important is missed. Our process is designed to find, assess, and reduce risks, including those related to mastering risk management in software development.
Phase 2: Analysis and Evaluation
Once we know what to protect, we look for potential dangers. In this phase, we analyze the threats that could harm your assets and the vulnerabilities in your setup that might let them in.
A threat is an outside danger, like a ransomware attack targeting local businesses. A vulnerability is an inside weakness, like an employee using an easy-to-guess password or a server that is missing security updates.
We look at how likely a threat is to happen and what the impact would be on your business. For example, a data breach at a small medical clinic in Seaside could lead to big government fines and a total loss of patient trust.
We don't just look for tech problems. We also look at human factors, like security awareness training, and process problems, such as your data backup plan. This gives us a full, 360-degree view of your risk.
Phase 3: Prioritization and Remediation Planning
The final phase brings everything together into a plan you can act on. We don't just give you a list of problems. We give you a prioritized roadmap for fixing them. We rank each risk based on its potential impact and the cost to fix it.
This is where our promise of "enterprise-level IT at an affordable price" really helps. We help you focus your time and money on the biggest issues first. This ensures you get the most security improvement for your investment.
Your final report will include clear, practical advice, such as:
- Immediate Actions: Urgent fixes for high-risk problems that need to be addressed right away.
- Short-Term Goals: Important improvements for the next few months, like setting up multi-factor authentication.
- Long-Term Strategy: Advice for future planning, like replacing old equipment or creating an official cybersecurity policy.
The result is a clear path forward—a practical, budget-friendly plan to secure your business and give you peace of mind.
Why Salinas Businesses Cannot Afford to Skip This

It’s one of the most common—and dangerous—myths we hear from local business owners: "I'm too small to be a target."
The reality is that cybercriminals often see small and mid-sized businesses as easy victims, because they assume security is not a high priority. Ignoring this risk is a gamble you can't afford to take.
The cost of a data breach isn't just about money. It's a direct hit to your reputation and the trust you've worked hard to build with customers here in the Monterey Bay area.
Investing in a cybersecurity risk assessment service is one of the smartest, most proactive steps you can take to protect your business. It’s not just an expense; it’s an investment in your company’s future.
More Than Just Preventing a Hack
While stopping a cyberattack is a huge benefit, the value of a risk assessment goes much deeper. It gives you a clear, strategic advantage that helps every part of your business, from your budget to your customer relationships.
Think about it in these practical terms:
- Build Unbreakable Customer Trust: Your customers, whether they're Monterey tourists or Salinas families, trust you with their information. Being proactive about security shows you value that trust and gives you a strong competitive edge.
- Create a Smarter IT Budget: Stop spending money on security tools you think you need. An assessment shows you exactly where your biggest risks are, so you can put your hard-earned money where it will have the most impact.
- Meet Industry Compliance Needs: Do you run a medical clinic in Seaside that must follow HIPAA rules? Or a financial services firm in Carmel with strict data rules? An assessment is the first step to making sure you meet those legal duties and avoid big fines.
A data breach can cost a small business thousands, or even millions, in recovery costs, fines, and lost business. A risk assessment is a small, affordable, proactive investment that helps you avoid that disaster.
This fits perfectly with our mission at Adaptive: providing enterprise-level IT strategy at a price that works for local businesses. You get the same level of protection as a large corporation, but designed for your specific needs and budget.
Understanding the True Cost of Inaction
The damage from a cyberattack lasts long after the event itself. The financial cost can be huge, but the damage to your reputation can be even harder to fix. Once customer trust is broken, it's very difficult to get back.
This is why the demand for cybersecurity risk assessment services is growing so quickly. The market was valued at USD 245.6 billion in 2024 and is expected to jump to USD 639.2 billion by 2032 as more businesses realize they need to be proactive. This growth is caused by more complex threats and stricter rules.
Understanding bigger rules, like the NIS2 cybersecurity directive, shows why these assessments are so important for business survival and staying legal.
For local companies, this isn’t just a global trend; it’s about the risks we all face here. You can learn more about the specific threats targeting companies in our community in our guide to Salinas business cybersecurity. Skipping an assessment means you're operating in the dark, hoping for the best while your most important assets are at risk.
Choosing the Right Cybersecurity Partner
Picking the right IT partner is a big decision for your business. This isn't just about finding someone to fix a computer. It's about finding a trusted advisor who understands your goals and wants you to succeed. So how do you find a provider who truly gets what it's like to run a business here in Monterey County?
It comes down to asking the right questions. You need a partner who sees you as more than just another client—someone who understands your role in the local economy, whether you’re in Salinas agriculture or Carmel hospitality.
Local Expertise Matters More Than You Think
A huge, national firm might have big-name clients, but do they really understand the unique challenges of running a business in our area? A local partner does. We live here and work here, which means we care about the health of our community.
That "local-first" approach gives you real benefits:
- Responsive Support: When a problem happens, you need help now, not in a few business days. A local team can give you faster, more personal support than a distant call center.
- Industry Knowledge: We have experience working with businesses in our area's key industries, like agriculture, hospitality, and education. We already understand how you work and the specific threats you face.
- A True Partnership: Our goal is to build long-term relationships. Your success is our success, and we're dedicated to giving you proactive advice to help your business grow safely. Learn more about our approach in our overview of professional IT services.
Key Questions to Ask Any Potential Provider
When you're looking at providers for cyber security risk assessment services, don't be afraid to ask tough questions. Their answers will tell you everything you need to know about their style and if they’re a good fit for you.
Use this checklist during your talks:
- Do you have experience with businesses like mine in Monterey County? This question quickly shows if they understand the local area and your industry's challenges.
- Can you explain your findings in plain English? The goal of an assessment is to get clarity, not more confusion. A great partner will explain technical stuff in a simple, easy-to-understand action plan.
- How do you adjust your services for a small business budget? This ensures they respect our mission of delivering "enterprise-level IT at an affordable price."
- What does your support look like after the assessment is done? The assessment is just the start. You need a partner who will help you put the advice into action and provide ongoing support.
Choosing a cybersecurity partner is like hiring a key member of your team. You want someone with the right skills, a deep understanding of your business, and a real commitment to helping you succeed. Don’t settle for less.
The need for these services is growing as digital threats get more complex. The global cybersecurity market is set to hit USD 351.92 billion by 2030. This is a clear sign that businesses everywhere are focused on risk assessment. For your Salinas or Seaside business, finding a local expert who can guide you is the smartest move you can make.
Frequently Asked Questions About Risk Assessments
If you’re busy running a business, the world of cybersecurity can feel a bit complicated. That's totally understandable. To help, we've gathered the most common questions we hear from local business owners about cyber security risk assessment services.
Here are some simple answers to give you a clearer picture of what the process involves.
How Long Does a Risk Assessment Take?
That’s a great question, and the honest answer is: it depends. A real assessment isn’t just a quick scan; it's a deep look into how your specific business works. For a typical small to mid-sized business here in Monterey County, the whole process usually takes from a few weeks to a couple of months.
Several things can affect that timeline:
- Business Size: A small shop in Pacific Grove has a simpler IT setup than a large farm operation in Salinas. The more parts there are, the more time we need.
- Complexity of Systems: The number of servers, computers, software programs, and cloud services you use plays a big role.
- Your Team's Availability: Our process is a partnership. The easier it is for us to talk to your key people, the faster everything goes.
We always provide a clear timeline from the start, so you know exactly what to expect.
What's the Difference Between a Risk Assessment and a Penetration Test?
This is a very common point of confusion, but the difference is important. Think of it like securing your home.
A risk assessment is like hiring a home security expert. They walk through your whole property, check every lock, inspect the windows, look at your outdoor lighting, and give you a detailed report on your overall security. It’s a big-picture review of where you're strong and where you're weak.
A penetration test (or "pen test") is like hiring someone to actively try to break into your house. Their only goal is to find a way in—whether that means picking a lock or forcing open a window. It's a focused test of your defenses against a real attack.
So, a risk assessment tells you where you’re weak, while a pen test confirms if a weakness can be used by an attacker. They're different but work together perfectly.
Is a Risk Assessment a One-Time Service?
Cybersecurity is never "one and done." Just like you service your company cars or review your finances each year, your security needs regular check-ups. We strongly recommend a full risk assessment at least once a year, or whenever your business makes a big change.
Think about it: new threats appear all the time, and your business is always changing. You might hire new people, add new software, or move more data online. Each of those changes can create new risks.
An annual risk assessment makes sure your security plan keeps up with both your business's growth and new threats. It’s a key part of smart IT management.
Regular assessments are also a vital part of any solid security plan. This proactive approach is essential for protecting your data, much like the strategies we cover in our guide to backup and disaster recovery solutions.
What Happens After the Assessment Is Finished?
Our work doesn’t stop after the analysis. In fact, that’s where the real value begins. We will never just hand you a technical document and wish you luck.
Instead, we give you a clear, easy-to-understand report that explains all the technical findings in plain English. Most importantly, we give you a prioritized action plan. This plan shows you what to fix now, what to work on next, and what to plan for in the future, all while keeping your budget in mind.
We'll walk you through every recommendation and help you take the first steps toward a safer and stronger future.
It's Time to Secure Your Business
You’ve put everything into building your business, and our job is to help you keep it safe. We've talked about a lot in this guide, from what a cyber security risk assessment service is to why it’s so important for companies right here in Salinas and across Monterey County. At the end of the day, this isn't about complicated tech—it's about smart, practical business planning.
Think of a risk assessment as more than just another item on your to-do list. It’s a key investment in your company’s future. It gives you the clarity to make smart decisions, the strategy to spend your IT budget wisely, and the peace of mind that comes from knowing you’re prepared. You can't afford to guess when your reputation and customer trust are on the line.
Your Local Partner in Cybersecurity
Your Salinas-based business is a vital part of our community. From the agricultural fields to the downtown shops, local companies are the backbone of our economy. That's why you deserve the same strong protection as large corporations, but with a local touch and at a price that makes sense for you.
Choosing to be proactive about cybersecurity is one of the most powerful decisions you can make. It sends a clear message to your customers and employees that you're serious about the long-term health of your business. We're here to make that process simple and effective for you.
Protecting your business starts with a single conversation. You don't need to be a technology expert to take control of your security—you just need a partner who is.
Let’s work together to build a stronger, more secure future for your company. Our team is ready for a friendly, no-pressure chat about your specific needs and worries.
Don't wait for a threat to make the first move. Contact Adaptive Information Systems today to schedule your consultation and learn how our cyber security risk assessment services can protect everything you’ve built.
Adaptive Information Systems
380 Main St, Salinas CA 93901 | 831-644-0300 | hello@adaptiveis.net
