As a business owner, your job is to run your company, not become a cybersecurity expert. But if you operate anywhere in the Monterey Bay area, from the agricultural heart of Salinas to the bustling hospitality scene in Carmel, understanding your digital risks is non-negotiable. This often starts with two terms that sound similar but are worlds apart: penetration testing and vulnerability scanning. Getting this right is the first step toward building a defense that protects your business without breaking your budget.
Think of it this way: vulnerability scanning is like a security guard making nightly rounds of your digital property. It’s an automated, routine check for known security flaws—testing all the doors and windows to see if they're unlocked. On the other hand, penetration testing is hiring an expert to actively try to break in. This simulated, human-led attack is designed to see if those unlocked doors and windows can actually be used to get inside and do real damage.
Vulnerability Scanning vs. Penetration Testing: The Two Sides of Security Assessment
For a business owner in Salinas or anywhere in Monterey County, your main job is running your company, not becoming a cybersecurity expert. But getting a handle on the difference between penetration testing and vulnerability scanning is a critical first step in building a solid defense. Both are meant to protect you, but they answer very different questions.
A vulnerability scan is fast and automated. It’s like a digital checklist, quickly scanning your systems for thousands of known weak spots and giving you a report. A penetration test (or "pen test") is where you hire an ethical hacker to actively try and break in. This shows you not just where the weak spots are, but how a real attacker could string them together to get inside and steal your data or disrupt your operations.
Choosing Your Cybersecurity Shield
To make the right call for your business, it helps to see these two approaches side-by-side. One gives you breadth and consistency, while the other delivers depth and real-world proof. For many local businesses in sectors like hospitality or professional services, understanding this trade-off is the key to creating a smart, affordable security plan. A strong defense often starts with finding the right partner, which is why choosing from the best IT service providers is so important.
Your security question shouldn't just be "Am I vulnerable?" It needs to be "What could an attacker actually do with those vulnerabilities?" Scanning answers the first question. Pen testing answers the second.
Here’s a quick breakdown of how they stack up:
| Criterion | Vulnerability Scanning | Penetration Testing |
|---|---|---|
| Methodology | Automated: Uses software to scan for a long list of known weaknesses. | Manual & Automated: A human expert simulates a real-world attack, using tools and creative thinking. |
| Goal | Find Vulnerabilities: Identifies and creates a list of potential security flaws. | Exploit Vulnerabilities: Proves if flaws can actually be used to breach your systems and cause harm. |
| Scope | Broad: Scans many systems for thousands of known issues very quickly. | Deep & Narrow: Focuses intently on specific targets to find a viable path in, just like a real attacker. |
| Frequency | High: Can be run monthly, weekly, or even daily for continuous monitoring. | Low: Usually performed once a year, or before a major system launch. |
| Cost | Affordable: A lower-cost service, perfect for routine security hygiene. | Investment: A higher cost due to the specialized, hands-on expertise required. |
Vulnerability Scanning: Your Automated First Defense
Think of vulnerability scanning as the foundational layer of your security—it’s your automated, ever-vigilant first line of defense. This process uses specialized software to systematically check your entire digital footprint for known weaknesses. It’s like having a security patrol that never sleeps, constantly checking your network, servers, and devices against a massive database of potential threats.
This automated approach is designed to be both broad and fast. For a busy agricultural business in Salinas or a small financial firm in Monterey, it provides a consistent, affordable way to maintain strong security hygiene without requiring constant manual effort from your team. The scanner’s job is to give you a clear, prioritized list of risks so you know exactly where to focus your attention first.
What Vulnerability Scans Look For
A vulnerability scan is essentially a health check for your IT environment. It methodically searches for common but critical security gaps that attackers love to exploit.
- Outdated Software: Scans will quickly identify unpatched operating systems, web browsers, or applications that have publicly known security holes.
- System Misconfigurations: This is a big one. The scan finds settings that were improperly configured, such as open ports or, even worse, default passwords that leave a door wide open.
- Missing Security Controls: It also checks for the absence of essential protections, like up-to-date antivirus software or properly configured firewalls.
The resulting report acts as a practical roadmap for remediation. It helps you tackle the most critical issues first, making your security efforts far more efficient and effective. Establishing this kind of routine check is a non-negotiable step we recommend for proactive, affordable protection, forming the backbone of any solid network security plan. You can explore more strategies in our small business guide to network security.
Vulnerability scanning is an automated process designed to rapidly identify known vulnerabilities across your systems. High-quality scanners can check for over 50,000 known weaknesses and are often required for compliance standards like PCI DSS.
This continuous process is crucial because it ensures ongoing security awareness. While it identifies potential weaknesses without attempting to exploit them, it offers an affordable way to keep your defenses up-to-date. By running these scans frequently—weekly or monthly—you create a strong, preventative security posture that is essential in today's threat environment.
Penetration Testing: Simulating a Real-World Attack
While a vulnerability scan gives you a list of potential weaknesses, a penetration test (or pen test) goes much further. It answers the one question that truly matters to your business: how much damage could an attacker actually do? This isn't a theoretical exercise; it's about putting your defenses to the test through the eyes of a real-world adversary.
Think of a pen test as the ultimate validation of your security measures. It’s a goal-oriented mission where a certified ethical hacker actively tries to breach your systems, mimicking the tactics a cybercriminal would use. They don’t just find a weak spot—they try to exploit it.
This human-led approach is what makes penetration testing so powerful. An ethical hacker brings creativity, critical thinking, and advanced tools to the table, uncovering attack paths that automated scanners could never see.
Uncovering the Real-World Impact
A pen test isn't designed to just hand you a long report of vulnerabilities. Its purpose is to demonstrate their actual business impact. For example, a tester might:
- Exploit a software flaw to get an initial foothold in your network.
- Move laterally through your systems to find more valuable targets.
- Attempt to access sensitive client data, financial records, or intellectual property.
This process reveals complex attack chains—a series of small, seemingly unrelated weaknesses that a skilled attacker can string together to create a major security breach. For a law firm in Carmel or a healthcare provider in Monterey, understanding these real-world risks is absolutely critical for protecting sensitive client information.
A penetration test shifts the focus from, "What vulnerabilities do I have?" to "Can these vulnerabilities be exploited to compromise my business?" It provides a true, qualitative assessment of your security posture.
The Human Element Is the Key Differentiator
Unlike automated scanning, penetration testing relies on the expertise of a security professional. These ethical hackers don't just follow a script; they adapt their strategy on the fly based on what they discover, mimicking the persistence and ingenuity of actual attackers.
They might use social engineering tactics, exploit subtle configuration errors, or find clever ways to bypass security controls. This manual, in-depth analysis provides priceless insights into how well your defenses hold up under the pressure of a determined attack. Ultimately, it gives you proof of exploitability, allowing you to prioritize fixes based on real, demonstrated risk instead of a long list of potential threats.
Comparing Key Differences for Your Business
Now that we've covered the "what" behind each approach, let's dig into the practical differences in the penetration testing vs. vulnerability scanning debate. As a business owner, understanding these distinctions is key to making smart, cost-effective security decisions for your company. The right choice really comes down to your specific goals, your budget, and the level of risk you're comfortable with.
The easiest way to think about it is with a simple analogy. A vulnerability scan is like a routine safety inspection for your office building. An inspector comes through with a detailed checklist, noting every potential hazard—a faulty wire here, a weak lock there.
A penetration test, on the other hand, is like hiring a professional team to actively try and break into that same building. They're not just checking for weak locks; they're trying to pick them, find an unlocked window, or talk their way past the front desk to prove they can get inside.
Methodology and Scope
The most fundamental difference between the two is how they work and what they cover.
-
Vulnerability Scanning is Automated and Broad. This process uses specialized software to cast a wide net, quickly checking your systems against a massive database of thousands of known vulnerabilities. The main goal is to give you a comprehensive inventory of potential weak spots across your entire network.
-
Penetration Testing is Manual and Deep. This involves a human expert—an ethical hacker—who thinks creatively to not only find but also exploit vulnerabilities. Instead of a broad scan, they perform a narrow, deep dive to prove whether a weakness can actually lead to a real-world breach. This hands-on approach is critical for uncovering complex flaws that automated tools almost always miss.
To help you decide which approach fits your needs, the table below offers a quick side-by-side comparison.
Vulnerability Scanning vs Penetration Testing At a Glance
| Criterion | Vulnerability Scanning | Penetration Testing |
|---|---|---|
| Primary Goal | Identify a broad list of potential vulnerabilities. | Prove the exploitability of vulnerabilities. |
| Methodology | Automated; relies on software and databases. | Manual; driven by human expertise and creativity. |
| Scope | Wide and shallow; covers many assets quickly. | Narrow and deep; focuses on critical assets. |
| Frequency | High (monthly or quarterly is common). | Low (typically annually or biannually). |
| Cost | Lower; often a fixed, recurring fee. | Higher; a significant, project-based investment. |
| Time Required | Fast; can take minutes to a few hours. | Slow; can take days or even weeks. |
| Best For | Routine security hygiene and compliance checks. | Simulating real-world attacks and assessing true risk. |
As you can see, these aren't interchangeable services. They are complementary tools designed for very different jobs.
Cost and Desired Outcome
Your budget and what you hope to achieve will be major factors in your decision. One gives you an affordable list of "what-ifs," while the other delivers priceless proof of "what could actually happen."
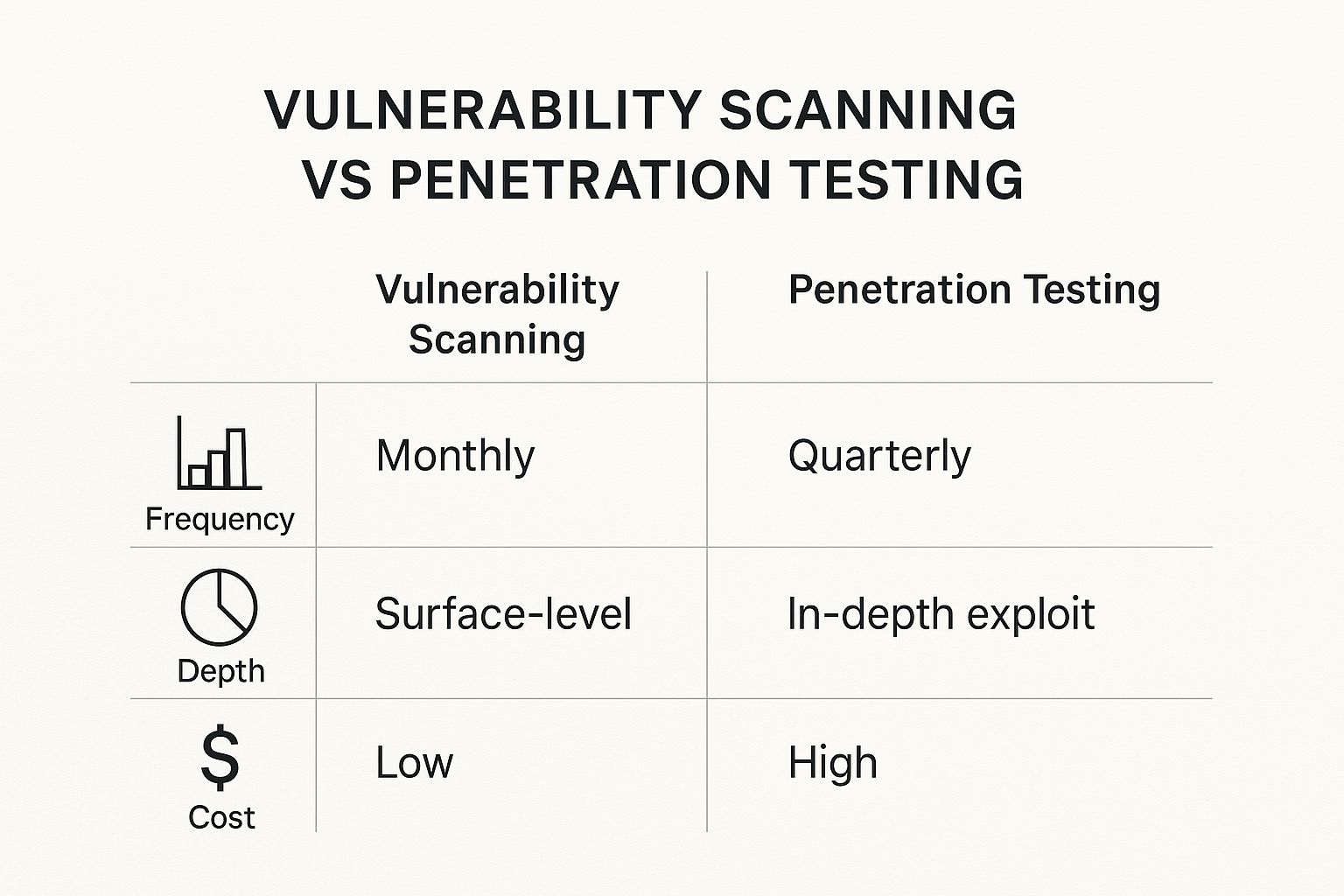
This infographic helps visualize the trade-offs in frequency, depth, and cost.
As the chart illustrates, vulnerability scanning is a low-cost, high-frequency activity you can do often. Penetration testing is a much deeper, more resource-intensive investment you make less frequently.
The core difference in outcome is simple: a vulnerability scan gives you a list of potential vulnerabilities, while a penetration test provides proof of exploitability. A scan might generate false positives, but a pen test validates which threats are real and demand immediate action.
This is a crucial distinction for any business in Monterey County, especially those in hospitality or agriculture that handle sensitive customer or operational data. A vulnerability scan might flag a hundred potential issues, but a pen test will tell you which one or two of those could actually allow an attacker to disrupt your business or steal your data.
This clarity helps you focus your limited time and resources where they'll have the biggest impact—which aligns perfectly with our mission of providing affordable, enterprise-level security to local businesses.
When to Choose Each Cybersecurity Approach
Deciding between a vulnerability scan and a penetration test isn't really an "either/or" situation. It’s more about knowing which tool to pull out of the toolbox for the job at hand. The right strategy for your business will depend on your specific needs, your risk profile, and any compliance rules you have to follow. Honestly, the best approach usually involves using both at different times as your business grows.
For a lot of growing businesses here in Marina or Seaside, the most practical and budget-friendly first move is to get into a routine of regular vulnerability scanning. This is how you build a solid security foundation, by constantly finding and patching known weak spots. Think of it as the essential, ongoing maintenance that keeps your digital doors and windows locked tight.
When to Start with Vulnerability Scanning
If you're just starting to build out your security program, consistent vulnerability scanning is your best friend. You’ll want to make this your priority if you're:
- Establishing a Baseline: You need a clear, full inventory of potential security holes across your network, but you don't have a huge budget for a massive upfront project.
- Meeting Basic Compliance: Many industry regulations, even the less strict ones, require regular scanning to show you're doing your due diligence and maintaining good security hygiene.
- Practicing Proactive Maintenance: You want an affordable way to stay on top of new threats as they emerge and make sure your software is always patched and configured correctly.
When to Invest in a Penetration Test
A penetration test is a much bigger investment, and it’s reserved for when you need to answer a more serious question: “Can a real attacker actually get in and do damage?”
Think of it this way: vulnerability scanning tells you a window latch is loose. Penetration testing sends an expert to see if they can actually jimmy that window open, climb inside, and crack your safe. That’s the level of assurance you need when the stakes are high.
It’s time to bring in the pros for a penetration test if your business:
- Handles Sensitive Data: A medical practice in Monterey, a law firm down in Carmel, or any business that manages personal or financial information has to know its defenses can hold up against a determined, targeted attack.
- Faces Strict Compliance Mandates: Regulations like HIPAA or PCI DSS don't just suggest security—they often require periodic penetration tests to prove your security controls are actually working as intended.
- Undergoes Major System Changes: Just launched a new application, moved your servers to the cloud, or completed a big network overhaul? A pen test is crucial to validate that those changes didn't accidentally introduce new, exploitable flaws.
Ultimately, these two services aren't competitors—they’re partners. A mature security strategy combines frequent, automated vulnerability scanning with periodic, in-depth penetration tests. This layered approach, guided by a solid risk analysis, creates a defense that can scale right along with your success. A great place to start is by using our guide to conducting a cybersecurity risk assessment to figure out what your most critical assets are.
Understanding the Cost and Return on Investment
For any small or mid-sized business, especially here in the Monterey Bay Area, every dollar has to count. When you start comparing the costs of penetration testing versus vulnerability scanning, you're not just looking at two different price tags. You're really evaluating two distinct types of investment in your company's security and future.
Vulnerability scanning is your high-ROI, budget-friendly foundation. Because the process is automated, it fits neatly into an ongoing operational budget without needing a ton of hands-on effort. This makes it an incredibly cost-effective way to maintain good security hygiene and show partners and clients you're taking security seriously.
The Investment in a Penetration Test
A penetration test, on the other hand, is a much more significant—but often critical—investment. The cost is a direct reflection of the deep expertise and the dozens of hours a certified ethical hacker spends simulating a real-world attack against your systems. This isn't a simple software subscription; it’s a project-based service that requires specialized, hard-to-find talent.
The financial and resource differences are stark. Vulnerability scanning is largely automated, which keeps human intervention and costs low. In contrast, penetration testing requires an expert to manually probe for and try to exploit weaknesses, a process that demands advanced tools and extensive time, which naturally drives up the price. You can explore more on this topic from Indusface.
While a pen test costs more upfront, a single, thorough test can uncover a critical flaw that, if exploited, could cost your business exponentially more in lost revenue, reputational damage, and recovery fees. It’s a vital investment in protecting your most valuable assets.
Balancing Cost with Compliance and Risk
Ultimately, making the right financial call comes down to balancing affordability with your specific risk profile and compliance mandates. While routine scanning is a must-have for just about every business, a penetration test becomes a necessary investment when you handle sensitive data or have to follow strict industry regulations.
For many businesses in regulated fields, pen tests aren't optional—they're required. If you're not sure where your business stands on this, our guide on cybersecurity compliance essentials can help spell out your obligations.
The key is to see both services not as expenses, but as smart investments in your business’s resilience and long-term success.
Your Partner in Monterey County Cybersecurity
Trying to get a handle on cybersecurity can feel overwhelming, but it’s not something you have to figure out on your own. Here at Adaptive Information Systems, our entire mission is to bring enterprise-grade IT solutions to local SMBs across Monterey County—at a price that actually makes sense for your budget.
Whether you're just looking to get routine vulnerability scanning in place or you need a full-blown penetration test to uncover hidden risks, we’re here to be your trusted advisor. We’ll help you make sense of your unique security landscape and build a practical, effective plan to protect the business you’ve worked so hard to grow.
For more insights on building a smart IT strategy, take a look at our guide on Monterey business IT support.
Adaptive Information Systems
380 Main St, Salinas CA 93901 | 831-644-0300 | hello@adaptiveis.net