If you're a business owner in Salinas, you’ve probably seen a dozen articles about cyber threats. The trouble is, most of that advice is dangerously out of touch. They all repeat the same tired tips like “use strong passwords,” while the threats themselves have become something else entirely. For businesses here in Monterey County, this outdated advice leaves you wide open.
Why Old Cybersecurity Advice Is Failing Local Businesses
As a business owner, your plate is already full. Whether you’re in agriculture, hospitality, or another local industry, your job is running the company, not becoming a cybersecurity guru. You rely on the so-called "best practices" to stay safe, but in 2025, that's just not cutting it anymore.
The reality is, the advice hasn't kept pace with the threats. Today’s attackers are using Artificial Intelligence (AI) to launch smarter, faster, and more precise attacks that blow right past old-school defenses. They aren't just guessing passwords anymore; they're cracking them in seconds.
The Widening Gap Between Perception and Reality
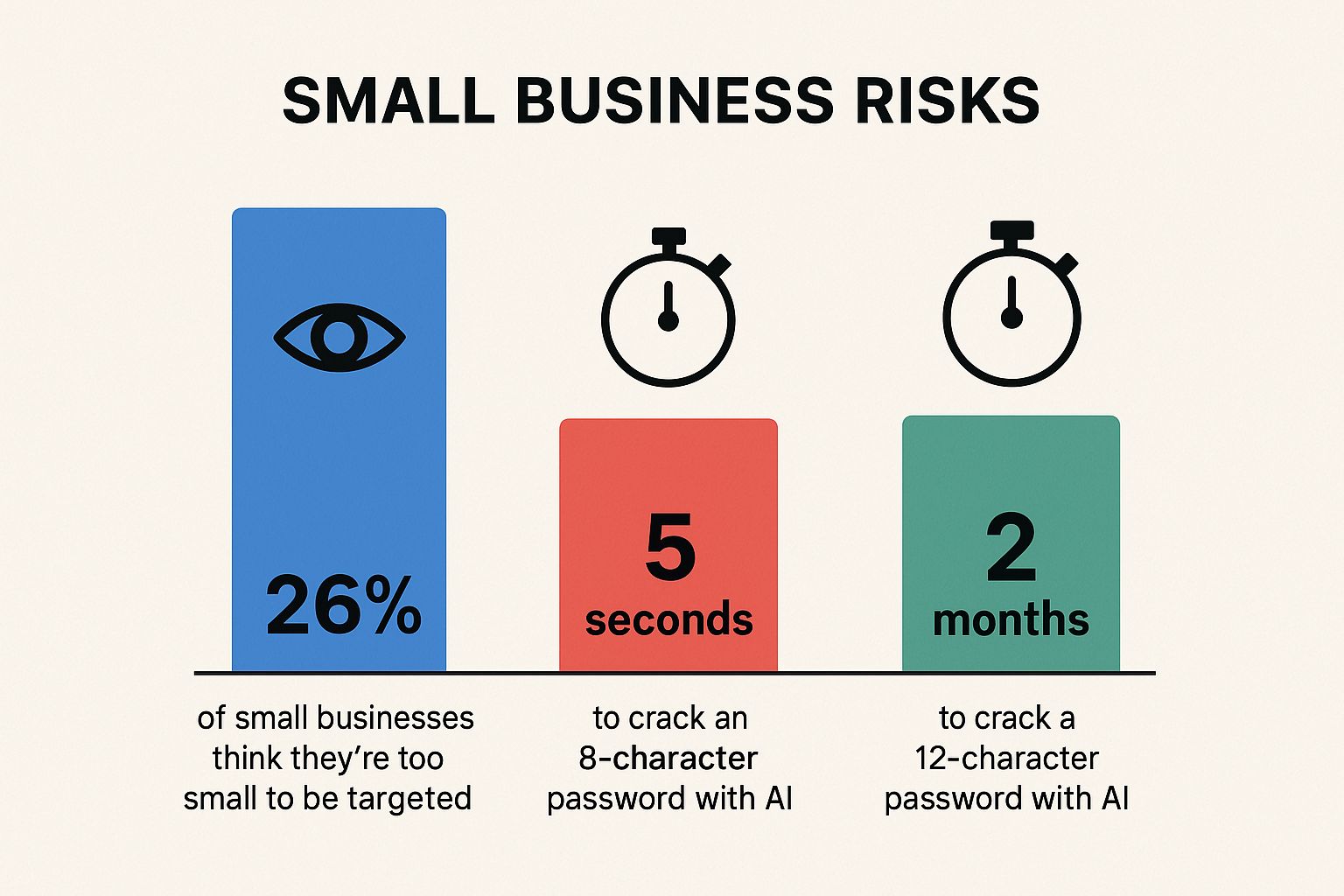
One of the biggest risks we see is a false sense of security. A recent report shows that 26% of small businesses still think they’re too small to be a target. This is a dangerous myth that puts local companies directly in the crosshairs. Hackers actually prefer small businesses because they know you're often running on basic, outdated security.
You can learn more about why hackers see small businesses as easy wins in our detailed guide.
This dangerous belief gets even worse when you see how quickly new tools have armed attackers. The infographic below shows the disconnect between this common myth and the stark reality of modern password-cracking speeds.
It's clear that what once passed for a "strong" password is now child's play for an AI-powered tool. This alone should tell you it’s time for a much more advanced approach to protection.
Beyond Passwords and Backups
Most of the advice out there stops at listing common threats like phishing and ransomware. They tell you to use complex passwords and back up your data, but that’s barely scratching the surface of what you actually need.
- Generic Advice: They give one-size-fits-all recommendations that don’t account for the realities of a hybrid workforce common in businesses from Carmel to Marina.
- Oversimplification: They miss the nuance of AI-powered phishing that can perfectly mimic an email from a trusted local supplier you've worked with for years.
- Fear-Based Messaging: A lot of articles just try to scare you into action without offering clear, empowering steps to actually get secure.
The table below breaks down just how flimsy some of this "best practice" advice really is against modern threats.
Outdated Advice vs. Modern Reality
| Outdated 'Best Practice' | The 2025 Threat It Misses | A Smarter Approach |
|---|---|---|
| Use complex passwords. | AI can crack even complex passwords in minutes, not days. | Implement Multi-Factor Authentication (MFA) and passwordless logins. |
| Just back up your data. | Ransomware now steals your data before locking it. | Adopt a Zero Trust approach and advanced endpoint security. |
| Train staff to spot phishing. | AI-driven emails are hyper-realistic, making them nearly impossible to spot. | Use AI-powered email filtering that analyzes behavior, not just text. |
As you can see, simply following the old playbook leaves massive security gaps. True security today requires a more intelligent, proactive strategy.
At Adaptive Information Systems, we're focused on clarity, not confusion. Our mission is to bring enterprise-grade security to your business in a way that’s affordable and grounded in the realities of operating in the Monterey Bay area.
It’s time to move past the checklist thinking that old articles promote. Real security in 2025 isn't about building higher walls; it’s about building a smarter defense that understands how attackers actually operate today.
The New Wave of Threats Targeting Local Businesses
It’s time to move past the old-school definitions of ‘phishing’ and ‘ransomware.’ While those threats haven’t gone away, the attacks themselves have evolved into something far more sophisticated. Attackers are now using tools that most generic security advice simply doesn't account for, leaving your business wide open.
Imagine this: an email lands in your inbox from a trusted local supplier here in Salinas. The tone is perfect, the details are spot-on, and there isn't a single typo. This isn't some clumsy scam; it's a message crafted by AI to be indistinguishable from the real thing.
This is the new reality of AI-enhanced phishing, and it completely changes the game. These AI tools can scrape public information about your company and your partners to build scams that are terrifyingly believable.
Beyond Just Email Scams
The threat doesn't stop with your inbox. Attackers are also using AI to generate convincing audio and video for what we call vishing (voice phishing) and deepfakes. A quick phone call with a deepfaked voice of your business partner could be all it takes to get an employee to authorize a fraudulent wire transfer.
These aren't futuristic threats; they are happening right now. And with 80% of SMBs planning to increase cybersecurity budgets, it's clear business owners are ready for real solutions, not just generic advice.
The Supply Chain Ripple Effect
Another massive threat that "best practices" checklists rarely mention is the supply chain attack. Think of all your software and service providers as a connected chain. An attacker doesn't need to break down your front door if they can slip through an unlocked window at one of your vendors.
Here's a local example: a single vulnerability in a popular vineyard management software used across Monterey County could compromise dozens of wineries at once. The attacker hits the software company, and the breach ripples down to every single client who uses that tool—including you.
Your security is no longer just about locking your own doors. It's now deeply tangled up with the security of every vendor, partner, and software provider you rely on. This interconnected risk is one of the biggest blind spots for small businesses today.
This is exactly where the old advice falls short. It focuses only on your immediate setup while ignoring the complex web of digital relationships that every modern business depends on. We break down the top 10 cybersecurity threats for 2025 in our other article, which goes deeper into these interconnected risks.
Making Sense of the Modern Threat Landscape
Understanding these new dangers is the first step toward building a defense that actually works. Here’s a quick rundown of what’s targeting businesses like yours:
- AI-Enhanced Phishing: Emails so personalized and well-written they sail right past human suspicion.
- Vishing and Deepfakes: Voice and video impersonations designed to trick employees into giving up sensitive information.
- Supply Chain Compromise: Breaches that start with your software vendors to gain backdoor access to your network.
These methods are built to exploit trust and bypass traditional security. They prove that just telling your team to "watch for bad grammar" is no longer enough. For a deeper look at building defenses, check out this comprehensive cybersecurity guide for small businesses. Your strategy has to evolve to counter the tools attackers are actually using.
How to Build Real Business Resilience Beyond Backups
For years, the gold standard of cybersecurity advice was simple: "back up your data." And while having backups is still absolutely critical, treating them as your only safety net is a dangerously outdated strategy in 2025. Today's threats have evolved, making a simple recovery far more complicated.
Modern ransomware attackers don't just lock your files anymore. Their new game plan is to quietly steal your sensitive data first, then encrypt your systems. This creates a painful two-pronged attack: they demand a ransom to unlock your files while simultaneously threatening to leak your confidential client information if you refuse to pay.
For a healthcare provider in Monterey or a law firm in Carmel, a data leak isn't just an inconvenience. It's a business-ending event that shatters client trust and triggers massive regulatory fines. This is exactly where the concept of cyber resilience becomes critical.
What Is Cyber Resilience
Cyber resilience isn’t just about blocking an attack or restoring files from a backup. It’s a complete strategy for operating through a security incident and getting your business back on its feet, fast. It’s about having a concrete plan to survive the initial hit and manage the chaotic aftermath that follows.
True resilience means you’re not just thinking about how to restore files. You're prepared for the tough questions: How will you communicate with clients? What are your legal obligations? How do you get your core operations back online in hours, not weeks?
A solid resilience plan moves way beyond just the technical side of the problem.
From Simple Backups to a Full Continuity Plan
A robust backup is just one piece of the puzzle. A true business continuity plan prepares you for the entire lifecycle of a cyber incident, ensuring every part of your organization knows exactly what to do when things go wrong.
This forward-thinking approach is critical as the financial stakes continue to climb. Global losses from cybercrime are projected to hit a stunning $10.5 trillion annually by 2025. This soaring cost has caused cyber insurance premiums to balloon, proving that simply trying to transfer risk is becoming an expensive—and often incomplete—solution. You can dig deeper into the growing financial risks of cybercrime at Cobalt.io.
A proper resilience strategy includes:
- Data Recovery Protocols: A clear, step-by-step process for restoring data from secure, isolated backups that attackers can't touch.
- Client Communication Templates: Pre-written statements to inform your customers about a breach transparently and confidently.
- Legal and Compliance Steps: A checklist of who to contact and what to report to meet regulatory requirements.
- Operational Continuity: A plan to keep essential business functions running, even if your primary systems are down.
Building this level of preparedness might sound like a job for a huge corporation, but it’s more accessible than ever for small businesses. You can explore our guide on developing effective business continuity solutions to see how these strategies can be scaled for your company. Responding to today's cyber threats is no longer just about buying the right software; it’s about having the right plan.
Securing Your Modern Hybrid Workforce
The way we work has changed for good. Across Pacific Grove and Seaside, businesses now have teams spread out everywhere—at home, in the office, and on the road. This flexibility is fantastic, but it completely shatters the old way of thinking about security.
For decades, cybersecurity was treated like a castle with a moat. You built a strong wall—your office firewall—to keep the bad guys out. But what happens when half your team is working outside the castle walls? That single firewall just doesn't cut it anymore.
The Problem with Old-School Security
The traditional approach runs on a dangerous assumption: everything inside your network is safe. This creates a massive blind spot. If an attacker tricks just one remote employee into giving up their password, they can slip right inside your "castle." Once they're in, the system trusts them, letting them move around freely.
This outdated model simply can't handle the reality of a modern workforce. An employee logging in from a coffee shop in Marina is just as vital to your business as someone at headquarters, and their connection needs to be just as secure.
Adopting a Zero-Trust Mindset
This is where a modern approach called zero-trust comes into play. Don't let the name intimidate you; the concept is simple but powerful.
Think of it like a secure government building. Just because you have a badge to get through the front door doesn't mean you can wander into every single room. At every interior checkpoint, a guard checks your ID and clearance again.
Zero-trust works the same way for your digital network. It operates on one core principle: "never trust, always verify."
A zero-trust framework assumes threats can come from anywhere—both outside and inside your network. It forces every single request for data or applications to prove its identity, no matter where that request comes from.
This constant verification dramatically shrinks an attacker's ability to cause damage. Even if they manage to steal a password, they can't move freely through your systems. They're stopped and re-verified at every turn.
Practical Steps to Implement Zero-Trust Security
Bringing this kind of enterprise-level security to your small business is more affordable and straightforward than ever. It’s not about buying one expensive piece of software; it's about applying a smarter security philosophy. Here are the core components:
- Multi-Factor Authentication (MFA) Everywhere: This is the foundation. Requiring a second form of verification—like a code sent to a phone—for every login blocks most password-based attacks.
- Verify Every Endpoint: Every device trying to connect to your network, whether it's a company laptop or a personal computer, must be checked and confirmed as secure before it gets access.
- Grant Least-Privileged Access: This one is huge. Employees should only have access to the specific data and applications they need to do their jobs, and nothing more. This policy drastically limits the potential damage if one of their accounts is ever compromised.
Adopting this framework is especially important now. Attackers are getting frighteningly good at exploiting the weaknesses in traditional security. You can explore more about the evolving threat landscape in this IBM report.
Securing a distributed team doesn't have to be a nightmare. With the right strategy, you can protect your data and empower your people to work safely from anywhere. To see how these concepts apply to businesses like yours, you can check out our guide on hybrid work security solutions.
Empowering Your People as Your Strongest Defense
Technology is only half the battle. Your firewalls and security software are essential, but at the end of the day, your team remains the true front line of your defense. Cybercriminals know this, which is why they overwhelmingly target people, not systems.
But the old approach to employee training—that boring, once-a-year video—is useless against modern threats. It treats your team like a liability to be managed rather than an asset to be empowered. In 2025, that mindset has to change.
From Annual Videos to Active Engagement
Effective cybersecurity training isn't a passive, one-time event. It’s an ongoing, interactive process that builds a strong security culture. This means ditching the generic slideshows and moving toward training that reflects the real-world threats your business faces every day.
Think of it this way: you wouldn't teach a firefighter by showing them a video of a fire once a year. You’d run drills and build muscle memory. Cybersecurity training needs the same hands-on approach.
Building a culture of security means creating an environment where an employee at a Watsonville non-profit feels confident reporting a suspicious email without any fear of blame. It’s about teamwork, not finger-pointing.
When your team knows they are a valued part of your defense, they become your best sensors for detecting threats. This cultural shift is one of the most powerful—and affordable—security upgrades you can make.
Making Training Practical and Relevant
The goal is to transform your team from a potential vulnerability into a powerful security asset. That requires a human-focused strategy that goes way beyond simple software checklists. Modern, effective training programs always include:
- Interactive Phishing Simulations: These aren't "gotcha" tests designed to trick people. They are safe, controlled drills that mimic the AI-enhanced phishing attacks targeting businesses right now, giving your team hands-on practice.
- Blame-Free Reporting: Create a simple, clear process for employees to report anything that seems off. When they do, thank them for their vigilance. That positive reinforcement is what encourages proactive behavior.
- Industry-Specific Scenarios: Training has to feel relevant. For an agricultural business in Salinas, this could mean simulating a fake invoice from a known equipment supplier. For a hospitality business, it might be a fraudulent booking confirmation.
This continuous cycle of practice, reporting, and positive feedback builds a resilient human firewall around your organization. To get a better handle on the specific tactics your team will face, you can review our guide on the growing dangers of email phishing.
The reality is, no technology is perfect. A clever attacker might eventually find a way past your filters, but they'll have a much harder time fooling a well-trained and engaged team. Investing in your people provides a return that no software alone can match.
Your Action Plan for Modern Cybersecurity
Knowing that cyber threats are evolving is one thing; doing something about it is another. Let's turn all this insight into a clear action plan to bring your security up to date. This isn’t about spreading fear—it’s about taking confident, practical steps to build real resilience for your business.
The first step is to assess your current defenses with a fresh perspective. Instead of just asking, "Do we have antivirus?" the real question is, "Are we prepared for a modern attack?" The goal is to move beyond a simple checklist and toward a smarter, more dynamic security posture.
A Modern Security Checklist
Use these points to see how your current strategy stacks up against the realities of 2025.
- Implement Multi-Factor Authentication (MFA) Everywhere: Is MFA active on every single application your team uses, from email to cloud storage? This remains your single most powerful defense against compromised passwords.
- Adopt Zero-Trust Principles: Do you operate on a "never trust, always verify" model? This means access to data should only be granted on a strict need-to-know basis, and every device must be verified before it connects.
- Conduct Ongoing Employee Training: Does your team participate in regular, interactive phishing simulations? A one-time training video is not enough. Training has to be a continuous process to keep pace with new attacker tactics.
- Document Your Incident Response Plan: Do you have a written plan for what to do during and after a breach? This should cover everything from technical data recovery to how you'll communicate with clients. A crisis is the wrong time to start figuring this out.
As part of your action plan, it's also crucial to review and understand your network configurations. This includes securely setting up port forwarding to prevent leaving unnecessary doors open for attackers.
Need a hand figuring all this out? The Adaptive Information Systems contact page offers a direct line to our local experts.
Ready to move from basic defenses to smarter, scalable cybersecurity? If you’re a small business in Salinas, Monterey, or Watsonville, connect with Adaptive Information Systems for guidance that’s grounded in your local reality and built for long-term resilience.
Adaptive Information Systems
380 Main St, Salinas CA 93901 | 831-644-0300 | hello@adaptiveis.net
Common Questions We Hear
We get it—cybersecurity can feel like a moving target, especially when most of the "best practices" you read online are already out of date for 2025. Here are some straightforward answers to the questions we hear most often from business owners just like you.
My Business Is Small. Are We Really a Target for Advanced Cyber Threats?
Yes, absolutely. In fact, hackers often prefer targeting small businesses precisely because they assume you have fewer security resources. They aren't picking you out by name; they're using automated tools to scan thousands of businesses at once, looking for any easy opening.
And it’s not just about your data. Criminals know you might be connected to larger clients. A breach at your company can become a digital stepping stone into a much larger organization in a supply chain attack. That makes you a very valuable target.
Isn't Antivirus Software Enough to Protect Us?
Antivirus was a great start… ten years ago. Today, it’s just one small piece of the puzzle. Traditional antivirus is designed to catch known, cataloged viruses—it looks for signatures it already recognizes.
The problem is, modern threats don't play by those rules. It won't stop a sophisticated phishing email or prevent a scam that exploits simple human error. A real defense is layered, combining tools like Multi-Factor Authentication (MFA) with ongoing employee training and a zero-trust mindset.
What Is the Single Most Important Security Step I Can Take Today?
Turn on Multi-Factor Authentication (MFA) everywhere you possibly can. This is, without a doubt, the single most powerful and effective action you can take right now. All MFA does is require a second check—like a code from your phone—before logging in.
It sounds simple, but this one step blocks the vast majority of password-based attacks. Even if a criminal manages to steal an employee’s password, they're stopped cold without that second code. It's a huge defensive win for very little effort.
How Much Does Modern Cybersecurity Cost for a Small Business?
It’s far more affordable and scalable than you might think. The old days of buying expensive on-site servers and software are gone. Modern, cloud-based security has brought top-tier protection within reach for small businesses, without the massive upfront investment.
The key is finding a partner who gets the realities of an SMB budget. You need a plan that tackles your biggest risks without trying to sell you a bunch of expensive extras you don't need. When you weigh that cost against the catastrophic expense of a breach, proactive protection almost always comes out way ahead.