If you're a business owner here in Salinas, the difference between vulnerability scanning vs penetration testing is pretty simple: one uses computers, and the other uses people. Think of vulnerability scanning as a fast, automated checkup that finds known security problems. Penetration testing, on the other hand, is a focused attack simulation where a real person—a professional "ethical hacker"—tries to break into your systems.
Understanding Your Security Options in Monterey County
As a local business owner, your data is one of your most important assets. It doesn’t matter if you’re protecting farm-to-table supply chain details in the Salinas Valley, guest information for a hotel in Monterey, or private client files; keeping that data safe is a must. Making smart, practical investments in your cybersecurity is what keeps you in business and ahead of the competition.
So, how do you get started? The first step is to understand the two main tools you have to check your defenses.
Part of building a solid cybersecurity strategy is knowing where you stand right now. A thorough technical due diligence checklist can give you that initial baseline and set the stage for more targeted security testing.
A Tale of Two Security Methods
Vulnerability scanning and penetration testing play very different, yet equally important, roles in keeping your business secure. One is a broad, automated sweep, and the other is a deep, manual dive.
A vulnerability scan is all about automation. It’s a tool that quickly scans your networks and systems, checking them against a huge list of known security flaws. A penetration test, or "pen test," is when you hire a skilled professional to actively try and use those flaws to see what a real attacker could actually do. This is why you ultimately need both: one gives you a wide view, while the other gives you the detailed, real-world proof you need to stop an attack before it happens.
For a lot of small businesses, creating a security plan from scratch can feel overwhelming. But having the right guidance changes everything. Our approach to Salinas business IT support focuses on building practical, affordable security plans that make sense for your company.
Key Takeaway: Think of it like this: a vulnerability scan is like your security alarm system telling you a door is unlocked. A penetration test is like hiring a security expert to see if they can actually pick that lock, get past the alarm, and crack open your safe.
Before we get into the details of each method, here’s a quick comparison to show you the main differences at a glance.
Quick Comparison Vulnerability Scanning vs Penetration Testing
This table gives you a simple summary of the key differences between these two essential security practices for your business.
| Attribute | Vulnerability Scanning | Penetration Testing |
|---|---|---|
| Approach | Automated, broad search for known flaws | Manual, focused attempt to exploit flaws |
| Goal | To create a list of potential weaknesses | To confirm if weaknesses can be used to break in |
| Frequency | High (weekly or monthly) | Low (once or twice a year) |
| Cost | Lower, more affordable for regular use | Higher, a significant one-time investment |
| Analogy | Checking every window and door for locks | Actively trying to break into the building |
Each approach has its place. Understanding when to use each one is key to building a defense that actually works for you.
Understanding Vulnerability Scanning: The Automated Checkup
Think of a vulnerability scan as your company's automated security patrol. It’s a software-driven process that checks your networks, servers, and applications against a huge, constantly updated database of known security weaknesses. For a busy hospitality business in Monterey or a professional services firm in Carmel, this is your essential first line of defense.
The main goals here are speed and coverage. A scan can quickly find common but critical issues—like unpatched software, weak passwords, or outdated systems—across your entire digital setup. This gives you a continuous, high-level report of your security health, letting you fix routine problems before anyone can use them against you.
How Automated Scans Work
Vulnerability scanners work by sending requests to your systems and then looking at the responses to find signs that match known security flaws. The whole process is automated and built to be efficient, casting a wide net to find potential problems.
The scanner then gives you a report that lists and prioritizes these potential issues, usually ranking them by how serious they are (like critical, high, medium, or low). This is exactly what your IT team needs to focus on fixing the most dangerous problems first.
For local businesses, regular vulnerability scanning is the most affordable way to maintain basic security. It's the digital equivalent of making sure all your doors and windows are locked every night—a simple but crucial practice.
This is your preventative maintenance for your digital systems. It helps you stay ahead of common threats without a major investment of time or money and answers the key question: “What are my known weaknesses?”
What Vulnerability Scans Typically Find
An automated scan is great at finding common, well-known security gaps—the kind of "low-hanging fruit" that attackers love to target first.
Here’s what they are great at finding:
- Missing Patches: It will quickly identify software, operating systems, or apps that are missing important security updates.
- Default Credentials: Scanners can easily spot systems still using factory-default usernames and passwords, which are a huge security risk.
- Service Misconfigurations: It flags services that are set up improperly, which could expose sensitive information to the public internet.
- Known Software Flaws: The scan checks against a massive library of common vulnerabilities and exposures (CVEs) to see if your systems are at risk.
While a general scan covers a lot of ground, specialized tools like a malware WordPress scanner can give you an extra layer of automated defense for your website. The reports from these scans are critical for your overall security planning. This constant cycle of scanning and fixing is fundamental to a strong defense and is a cornerstone of our mission to provide enterprise-level IT at an affordable price for local SMBs.
Understanding Penetration Testing: The Real-World Attack Simulation
If automated scanning is your routine security patrol, then penetration testing (or "pen testing") is like hiring a team of ethical hackers to actively try and break through your defenses. This goes way beyond a simple checklist of known problems. Instead, it simulates a real-world attack on your business to see how your security holds up under actual pressure.
This is the core of the vulnerability scanning vs penetration testing debate. While a scanner looks for known flaws, a human expert thinks creatively. They will try to combine several small, low-risk issues to create a major security breach—something an automated scanner simply can't do.
The Human Element in Cybersecurity
A penetration test is driven by human intelligence, not just software. The goal is to act like a real attacker, which involves a lot more than just running a program.
Ethical hackers use a variety of techniques to really test your defenses, including:
- Social Engineering: Trying to trick your employees into giving away sensitive information.
- Custom Exploits: Developing new ways to take advantage of unique flaws in your systems.
- Lateral Movement: Simulating how an attacker, once inside, would move through your network to find valuable data.
A pen test doesn't just ask, "Are there security holes?" It answers the more important question: "What could a determined attacker actually do with the security holes we have?"
This manual, in-depth approach is what makes penetration testing so valuable. It proves whether your security tools are truly effective against a thinking, adapting person.
Real-World Impact and Strategic Insights
The statistics on successful cyberattacks are a bit scary. For instance, recent data showed that in professional tests, hackers breached the network in a shocking 96% of companies. Even more concerning, once inside, they gained full control of the company's systems in 100% of cases.
These numbers show exactly why pen testing is so important. The final report you get isn't just a list of flaws; it's a strategic plan. It tells you exactly how an intruder could get in, what data they could steal, and the specific steps you need to take to strengthen your defenses. For any local Monterey business, this kind of insight is crucial for building a truly strong defense.
A proactive approach is always best. Understanding the complete picture of your defenses is a key part of any effective strategy. Check out our guide on Monterey cybersecurity to learn more about creating a layered defense that protects your critical assets. This human-led testing provides the proof you need to ensure your investments in security are actually working.
Comparing Key Differences: Scope, Frequency, and Cost
To build a security strategy that works without breaking your budget, you have to be clear on how vulnerability scanning and penetration testing really differ. The core of the vulnerability scanning vs penetration testing debate comes down to one thing: their approach. Scanning is automated and wide; pen testing is manual and deep.
This basic difference directly impacts their scope, how often you should run them, and what they will cost you. Let's look at these key areas so you can put your resources where they’ll do the most good for your business.
Scope of Analysis: Breadth vs. Depth
The classic comparison here is perfect. A vulnerability scan is often called "a mile wide and an inch deep." It's built to quickly check your entire digital footprint—every server, workstation, and connected device—for a huge list of known, common security flaws. It gives you broad coverage.
On the other hand, a penetration test is "an inch wide and a mile deep." Instead of scanning everything, it focuses on a specific target or system. A pen tester simulates a real-world attack to see just how far an intruder could get, diving deep into complex attack methods that an automated scanner would never see.
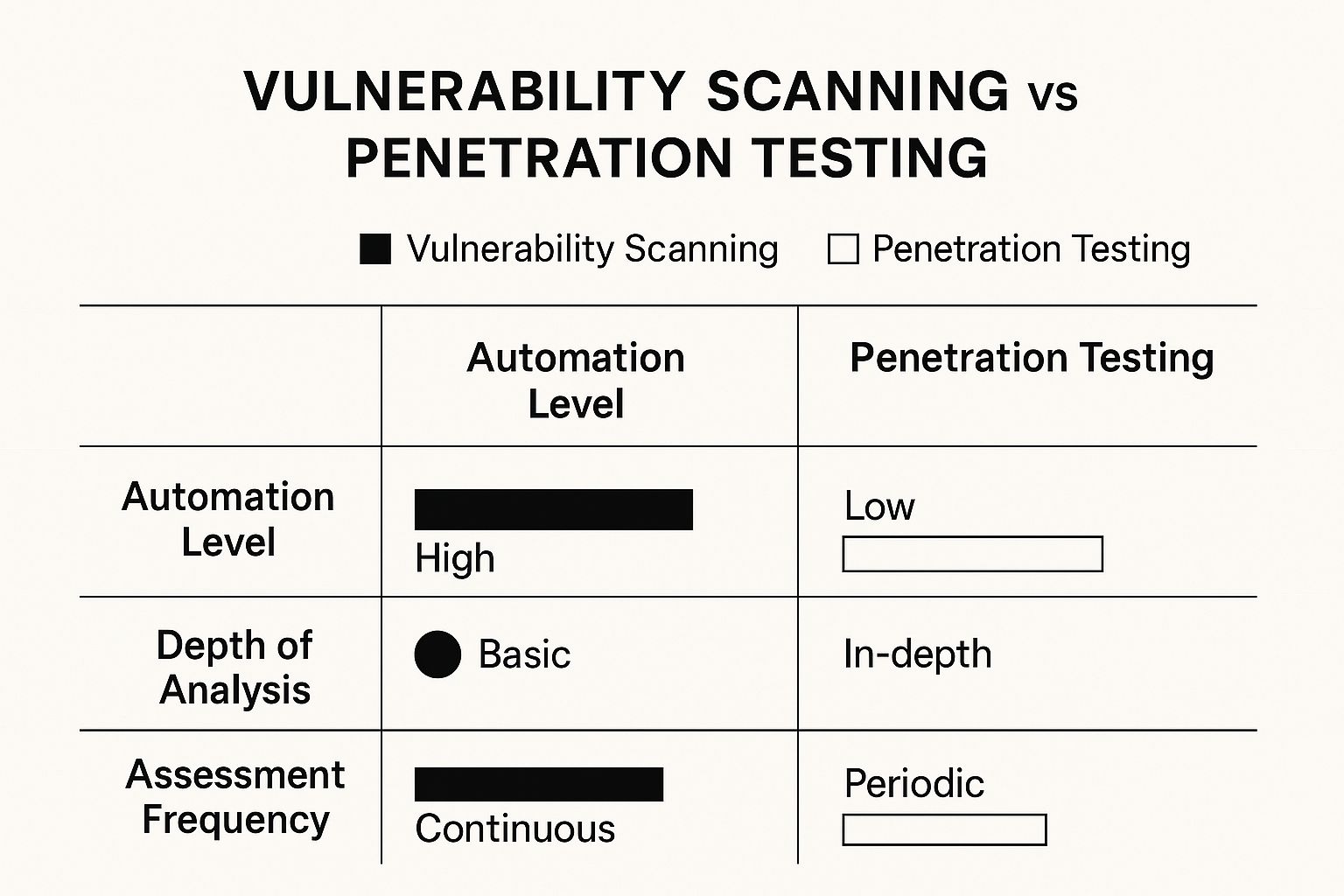
This visual breakdown shows the core differences in automation, depth, and frequency.
As you can see, scans offer continuous but surface-level coverage. Pen tests provide periodic, in-depth proof that your defenses are actually working.
Frequency and Timing of Assessments
Because they are so different, you'll use these two services on completely different schedules. Automated scans are meant to be run often and consistently. For most businesses in Monterey County, running scans on a monthly or even weekly basis is a smart, proactive move. It gives you a constant pulse on your security.
Penetration testing is a much bigger project. It's a serious investment in an expert's time and creativity, which makes it impractical to run all the time.
Think of a pen test like a major financial audit or a strategic stress test for your security. You’ll typically schedule one annually, right before launching a critical new application, or after making significant changes to your IT systems.
This difference in frequency is crucial. Scans are your ongoing maintenance, while pen tests are the periodic, deep-dive checks of those defenses.
Cost and Resource Investment
It's no surprise that the differences in approach and frequency lead directly to cost—a huge factor for any local SMB. Vulnerability scanning is, by far, the more affordable option. Since it's an automated process, the price is much lower, making it accessible enough for you to use regularly without hurting your budget.
Penetration testing is a premium service. You’re not just buying software; you're paying for the specialized skills and time of an ethical hacker. A single pen test represents a much larger investment.
Here's a quick, practical look at how these services stack up against each other.
Detailed Breakdown: Scanning vs Pen Testing
| Criteria | Vulnerability Scanning | Penetration Testing |
|---|---|---|
| Methodology | Automated; uses software to check for known vulnerabilities from a database. | Manual & Automated; human-led, using creative thinking and tools to simulate real attacks. |
| Scope | Broad; covers a wide range of assets to find many common, known issues ("mile wide, inch deep"). | Narrow & Deep; focuses on specific targets to uncover complex, unknown vulnerabilities ("inch wide, mile deep"). |
| Purpose | Identify known vulnerabilities and maintain security health. | Exploit vulnerabilities to see the real-world business impact and test defenses. |
| Frequency | High; typically run weekly, monthly, or quarterly. | Low; typically run annually, or for major system changes. |
| Cost | Low; often a recurring operational expense. | High; usually a project-based capital expense. |
| Required Skill | Low; can be run by an internal IT team with minimal training. | High; requires a certified ethical hacker with specialized expertise. |
Ultimately, it’s not about choosing one over the other. The goal for local businesses, from agricultural operations in Salinas to professional services in Pacific Grove, is to combine both into a layered strategy. This balanced approach ensures you catch the everyday issues with scanning while also preparing for the sophisticated, real-world attacks that only a pen test can uncover.
When to Use Each Cybersecurity Service
Deciding between vulnerability scanning and penetration testing isn't an "either/or" choice. It's about knowing when to use the right tool for the job to get the most out of your security budget. Understanding the specific situations where one service is better than the other is the key to building an effective—and affordable—defense for your business.
Think of it this way: vulnerability scanning is your routine, proactive security maintenance, like a regular health check-up. In contrast, penetration testing is more like a specialist you bring in before a major event.
Choosing Scans for Regular Security Hygiene
For most businesses, whether you're a nonprofit in Seaside or a legal firm in Monterey, vulnerability scanning should be a scheduled, recurring part of your IT operations. It's the foundation of a modern security program, built for consistency and frequency.
You should schedule a vulnerability scan in these common situations:
- On a Consistent Schedule: Running automated scans monthly or quarterly is a non-negotiable best practice. This creates a continuous baseline of your security and helps you catch new threats as they appear.
- After Minor System Updates: Any time you patch a server, update software, or add a new computer to your network, a quick scan can confirm the changes didn't accidentally open a new security hole.
- To Meet Basic Compliance: Many industry regulations require regular vulnerability assessments to prove you're actively managing security risks.
The real power of scanning is its ability to give you broad, systematic coverage. High-quality vulnerability scanners can check for over 50,000 known weaknesses, making them essential for meeting the demands of frameworks like PCI DSS and maintaining good security. You can discover more insights about compliance requirements on SecurityMetrics.com.
This ongoing process ensures you’re always aware of the easy targets that attackers love to hit first. It’s a must-have, affordable way to manage your day-to-day risk.
Deploying Pen Tests for Critical Validation
Penetration testing is your strategic weapon. It isn't for everyday use; it's for those moments when you absolutely must know if your defenses can stand up to a real, human-led attack. It answers the one question a scan can't: "Can a skilled attacker actually break through our defenses?"
You should bring in a penetration tester for these high-stakes situations:
- Before a Major Launch: Are you rolling out a new e-commerce website, customer portal, or app? A pen test is crucial to make sure it’s secure before it goes live and starts handling real customer data.
- After Significant Network Changes: If you've just moved to the cloud, redesigned your network, or added a major new system, a pen test proves that the new setup is truly secure.
- For High-Stakes Compliance: Regulations like PCI DSS (for handling credit cards) specifically require annual penetration testing. This goes far beyond what a simple scan can provide, offering the in-depth proof needed to satisfy strict auditors.
Let’s take a logistics company in Marina, for example. They would use monthly vulnerability scans to keep their servers patched and properly set up. But before launching a new supply chain portal connecting them with dozens of partners, they would invest in a penetration test. The test would simulate how an attacker might breach that portal to disrupt operations or steal shipping data, giving them confidence that their critical new system is genuinely secure.
For a deeper look at building this kind of layered defense, check out our guide on Salinas business cybersecurity. Using pen testing strategically like this provides the highest level of assurance precisely when you need it most.
Building an Affordable Security Strategy for Your SMB
Getting enterprise-level security on an SMB budget isn't about buying the most expensive tools—it's about building a smart, layered defense. When it comes to vulnerability scanning vs penetration testing, the smartest move isn’t choosing one over the other. It’s combining them to protect your business without setting your budget on fire.
For a local company here in Monterey County, this balanced approach delivers the best return on your security investment. The key is to think in layers, starting with the most affordable and consistent protection first.
Start with Frequent Automated Scanning
Your first layer—your foundation—should be frequent, automated vulnerability scanning. It’s by far the most cost-effective way to get a continuous read on your security. Think of regular scans as your digital alarm system, constantly checking for common weak spots like unpatched software or sloppy settings that attackers love to exploit first.
By running scans weekly or even monthly, you establish a baseline for your security. This simple, proactive step lets your team find and fix the easy-to-find problems before they turn into a real crisis, all for a predictable, manageable cost.
The goal of a layered strategy is simple: use the wide net of scanning for ongoing maintenance and reserve the deep-dive of penetration testing for your most critical systems. This protects your business without exceeding your budget.
Invest Strategically in Penetration Testing
Next, you bring in the specialists: periodic penetration testing. As an SMB, you likely don’t need to—and frankly, shouldn't—test your entire system at once. The cost would be huge. Instead, you need to focus your budget where it truly matters most.
Pinpoint your most critical assets and put them at the top of the list for testing. These are the systems that, if broken into, would cause the most damage to your business.
- Customer Data Systems: Any server or application that stores sensitive client information.
- Payment Processing Portals: Systems that handle credit card transactions or other financial data.
- Intellectual Property: The servers containing your unique business plans, trade secrets, or proprietary formulas.
By focusing your pen testing budget on these high-value targets, you get the maximum impact for your spending. You’re proving the security of the systems that are most important to your operations and reputation. To really lock things down, it’s also wise to implement essential data security best practices to complement your technical security services.
A Practical Approach for Local Businesses
When you pair the broad, consistent coverage of scanning with the focused depth of pen testing, you create a strong defense that’s actually practical. It’s a strategy that provides real security without the enterprise-level price tag.
This smart, layered approach is central to how we provide managed IT support in Salinas, ensuring local businesses get powerful protection that makes financial sense. You’re not just checking boxes; you're building a security program that can stand up to real-world threats and protect what you’ve worked so hard to build.
Adaptive Information Systems
380 Main St, Salinas CA 93901 | 831-644-0300 | hello@adaptiveis.net
Frequently Asked Questions
As an IT partner for local businesses, we get a lot of great questions about vulnerability scanning and penetration testing. Here are the answers to some of the most common ones we hear from business owners just like you.
Can I Just Choose One Service Instead of Both?
While having one is certainly better than having none, they really aren't interchangeable. Each service is designed to answer a different, vital question about your security.
Vulnerability scanning answers, "What are my known weaknesses?" A pen test answers, "Can an attacker use those weaknesses to cause real damage?"
Relying only on scanning leaves you blind to how several small flaws could be combined in a real-world attack. But relying only on penetration testing is far too expensive for continuous monitoring and will miss the day-to-day security gaps that pop up. The best practice is to combine frequent, affordable scanning for ongoing health checks with periodic, in-depth pen testing to prove your defenses work.
How Long Does Each Security Test Take?
The time commitment is another key difference in the vulnerability scanning vs penetration testing debate, and it's a huge factor for most businesses.
A vulnerability scan is automated and moves fast. Depending on the size of your network, a typical scan can be done in just a few minutes to a few hours.
A penetration test, on the other hand, is a much more involved, manual project. It includes planning, research, active testing, and detailed reporting. A full pen test usually takes anywhere from one to four weeks to complete from start to finish.
Are Both Required for PCI DSS Compliance?
Yes. If your business processes credit card payments, the Payment Card Industry Data Security Standard (PCI DSS) requires you to use both. For compliance, they are not optional or interchangeable.
- Requirement 11.2 of the standard calls for regular vulnerability scans. You must scan at least quarterly and after any significant change to your network.
- Requirement 11.3 calls for penetration testing. A pen test is required at least once a year and also after any significant changes.
This just goes to show how industry standards view these two services: as distinct but equally necessary layers of a strong security program.
For any business in Salinas or Monterey that handles cardholder data, meeting these PCI DSS requirements is non-negotiable. Both scanning and testing are essential for protecting your customers and your business.
How Are the Final Reports Different?
The final report you get from each service is tailored to its specific goal, and they look completely different.
A vulnerability scan report is an automated, often long, list of potential weaknesses found across your systems. These findings are typically ranked by a severity score (e.g., Critical, High, Medium) to help your IT team prioritize what to fix first.
In contrast, a penetration test report is a custom, strategic document. It reads more like a story, detailing the exact attack methods the ethical hacker used, explaining which vulnerabilities were successfully used, and showing what sensitive data was accessed. Most importantly, it gives you tailored, strategic recommendations to improve your overall security against real-world threats.
Adaptive Information Systems
380 Main St, Salinas CA 93901 | 831-644-0300 | hello@adaptiveis.net