If you run a business in Salinas or anywhere in Monterey County, you’re busy. You’re focused on your customers, your products, and your profits. Whether you're in the agriculture fields, a busy hospitality spot, or a local shop, you don’t have time to be a cybersecurity expert. That makes sense, but it can also be a problem. A few wrong ideas about technology could put everything you've worked for in danger.
Many local business owners in places like Monterey and Seaside think they are safe from hackers because of their size. This false sense of security leads them to not invest enough in protecting their business. Thinking “you’re too small to be hacked?” is the most common myth we see. As online attacks increase, these old beliefs are no longer just wrong—they're expensive risks.
This article will break down five of the most dangerous IT myths. We'll give you clear, simple advice to help protect your company. Let’s look at the facts and build a stronger, safer future for your business.
1. Myth #1: “We're Too Small to Be a Target”
This is the most dangerous idea a small business owner can have. It doesn't matter if you run a small shop in Carmel-by-the-Sea or a family farm in the Salinas Valley. Believing you are "flying under the radar" of hackers is a big mistake. The truth is, hackers often see small businesses as easy targets.
Thinking you’re too small to be hacked is a common but risky myth. Hackers use automatic tools to scan the internet for any weakness, no matter how big or small the company is. Your business isn't a tiny fish in a huge pond. To a hacker, you're an easy way to make quick money.
Why Your "Small" Business is a Prime Target
Hackers love going after small and mid-sized businesses (SMBs). First, they know you probably don't have a lot of money set aside for security. Second, you have data that is very valuable. This includes more than just credit card numbers:
- Customer Lists: Names, emails, and phone numbers can be sold or used for fake email attacks.
- Employee Records: Social Security numbers and payroll information are perfect for identity theft.
- Financial Data: Bank account details and client invoices can be used to steal money directly.
- System Access: If hackers get control of your computers, they can use ransomware to lock your files and demand you pay to get them back.
“Thinking your business is too small to matter is exactly why you become a target. Cybercriminals are counting on you to believe that.”
The Data Doesn't Lie
The facts are clear. A recent report from Verizon showed that 43% of all online attacks target small businesses. Our own Q4 2025 report found that 26% of small businesses still think they are too small to be hacked, even though 79% have been attacked in the last five years.
These attacks are not complex. They are often simple strikes that take advantage of common problems like weak passwords, old software, or an employee clicking on a bad link. The hacker’s software doesn't know you’re a local Monterey business; it just knows it found an unlocked door. The damage can be huge, causing financial loss, hurting your reputation, and stopping your business from running. Protecting your company starts with knowing that you are a target. Learn more about the specific cybersecurity threats facing small businesses and how to build a stronger defense on adaptiveis.net.
2. Myth #2: “Having a Firewall or Antivirus Is Enough Protection”
Putting in a firewall and antivirus software is a good first step. But it’s a big mistake to think that's all you need. This common belief is like locking your front door but leaving all the windows open. For business owners from Monterey to Salinas, relying only on these basic tools gives a false sense of security that modern hackers know how to beat.
Today's online threats are much more advanced than what old antivirus and firewalls can handle. These tools are a starting point, not the whole solution. They are good at catching known viruses but often miss newer, smarter attacks that trick your employees into letting them in. Thinking you are safe just because you have these tools is a major myth that leaves your business open to attack.
Why You Need More Than One Layer of Defense
A modern cyberattack is rarely just one thing. It's a chain of events, and your goal is to break that chain. Relying on only one or two defenses is a gamble. For example, in the big 2013 Target data breach, hackers got in by stealing login information from an outside company that managed the air conditioning. The firewall was working, but it couldn't stop an attack that looked like it was coming from a trusted source. A multi-layered defense is the only way to be safe. This means protecting your business at every level:
- Network Level: Firewalls and systems that watch for strange activity.
- Computer Level: Advanced antivirus tools that look for suspicious behavior, not just known viruses.
- Software Level: Keeping your programs updated to close security holes.
- Data Level: Using encryption to scramble your data so others can't read it.
- Human Level: Training your team to spot fake emails and other tricks.
“Antivirus and firewalls are like the seatbelts in your car. They are essential, but they won’t protect you in every type of crash. You still need airbags and good brakes.”
From Basic Tools to a Strong Defense
Moving beyond the "set it and forget it" myth means building a smart, proactive defense. This doesn't have to be complicated or expensive, even for a small agricultural business in the Salinas Valley. It starts by understanding that your firewall and antivirus are just the beginning.
Modern threats are designed to get around basic antivirus. A complete security plan includes tools that spot unusual behavior, keeps different parts of your network separate to stop an intruder from moving around, and regular security checks to find and fix weak spots. Building a truly secure network needs a complete view. Learn more about the specific network security best practices that create a robust defense at adaptiveis.net.
3. Myth #3: “We Only Need IT Support When Something Breaks”
Many small business owners think of IT support like a plumber—you only call when there’s a leak. This "break-fix" approach might seem like it saves money, but it's one of the most expensive IT myths in the long run. Waiting for a disaster, like a server crash or a data breach, means you're always playing catch-up.
Reactive IT support leaves your business vulnerable. By the time you notice a problem, the damage is already done. Your team can't work, customers are unhappy, and your reputation is on the line. Proactive IT support, like the managed services we provide, is about preventing problems before they start. It keeps your business running smoothly and securely, so you can focus on what you do best.
Why Waiting for a Crisis is a Bad Strategy
Relying on break-fix IT support is like only going to the doctor when you're having a heart attack instead of getting regular check-ups. Here’s why it’s a risky plan:
- More Downtime: When a system fails, your business stops. Every minute you're down costs you money and customer trust.
- Higher Costs: Emergency repairs are always more expensive than planned maintenance. You’ll pay premium rates for a quick fix, and the total cost of the disaster is often huge.
- Security Risks: Waiting until you’re hacked means the criminals have already won. They’ve had time to steal your data, damage your systems, and lock you out.
- No Long-Term Plan: Break-fix support doesn't help you plan for the future. You’re not getting advice on how to use technology to grow your business or stay ahead of new threats.
“Thinking of IT support as just a repair service is an outdated view. Today, smart IT is about keeping you safe, efficient, and ready for what’s next.”
The Data Doesn't Lie
Studies show that businesses that use proactive, managed IT services experience significantly less downtime than those that use a break-fix model. One report found that unplanned downtime can cost a small business up to $8,600 per hour.
For a local business in Salinas or Monterey, this could mean a server crashing during your busiest season. By the time you get a technician to fix it, you've lost thousands in sales and frustrated your customers. A proactive plan with 24/7 monitoring catches small issues before they become big disasters. Find out more about how to prepare for the worst by exploring the fundamentals of data backup and disaster recovery on adaptiveis.net.
4. Myth #4: “Our Data Isn’t Valuable Enough to Steal”
Another dangerous idea for a small business owner is thinking your company's data isn't worth anything to criminals. Whether you run a popular restaurant in Monterey or a busy farm supply company in Salinas, it’s easy to think hackers only want credit card numbers. The truth is, almost all business data can be bought, sold, or used for harm.
The myth that your data isn’t valuable is a huge blind spot. Hackers have created online black markets where every piece of information, from a customer email list to an employee's hire date, has a price. To them, your data isn't just information; it's a product they can sell.
Why Your "Worthless" Data is a Goldmine
Cybercriminals target small business data because it is often easy to get and can be used in many ways. What you see as simple business data, they see as valuable puzzle pieces:
- Customer and Client Lists: Names, emails, and phone numbers are sold in large groups for spam and fake email campaigns.
- Employee Records: Social Security numbers and addresses are used to commit identity theft or file for fake unemployment benefits.
- Business Information: Details about your vendors or clients can be sold to your competitors.
- Login Information: Employee usernames and passwords can be used to attack other, larger companies you work with.
“Thinking your data isn't valuable is like leaving your shop’s back door unlocked. You might think there’s nothing worth stealing, but a thief will always find something to take.”
The Data Doesn't Lie
The online market for stolen data is huge. A small doctor's office patient list can sell for a lot of money because it can be used for insurance fraud. Even a simple list of business contacts can be sold to spammers.
Hackers don't need to hit one big jackpot. They make money by gathering small amounts of data from thousands of businesses like yours. They use automatic tools to find unprotected files and servers, copy the information, and sell it. Protecting your data isn't just about following rules; it’s about protecting the core of your business. Learn more about how to protect against the evolving cyber threats that make your data a prime target on adaptiveis.net.
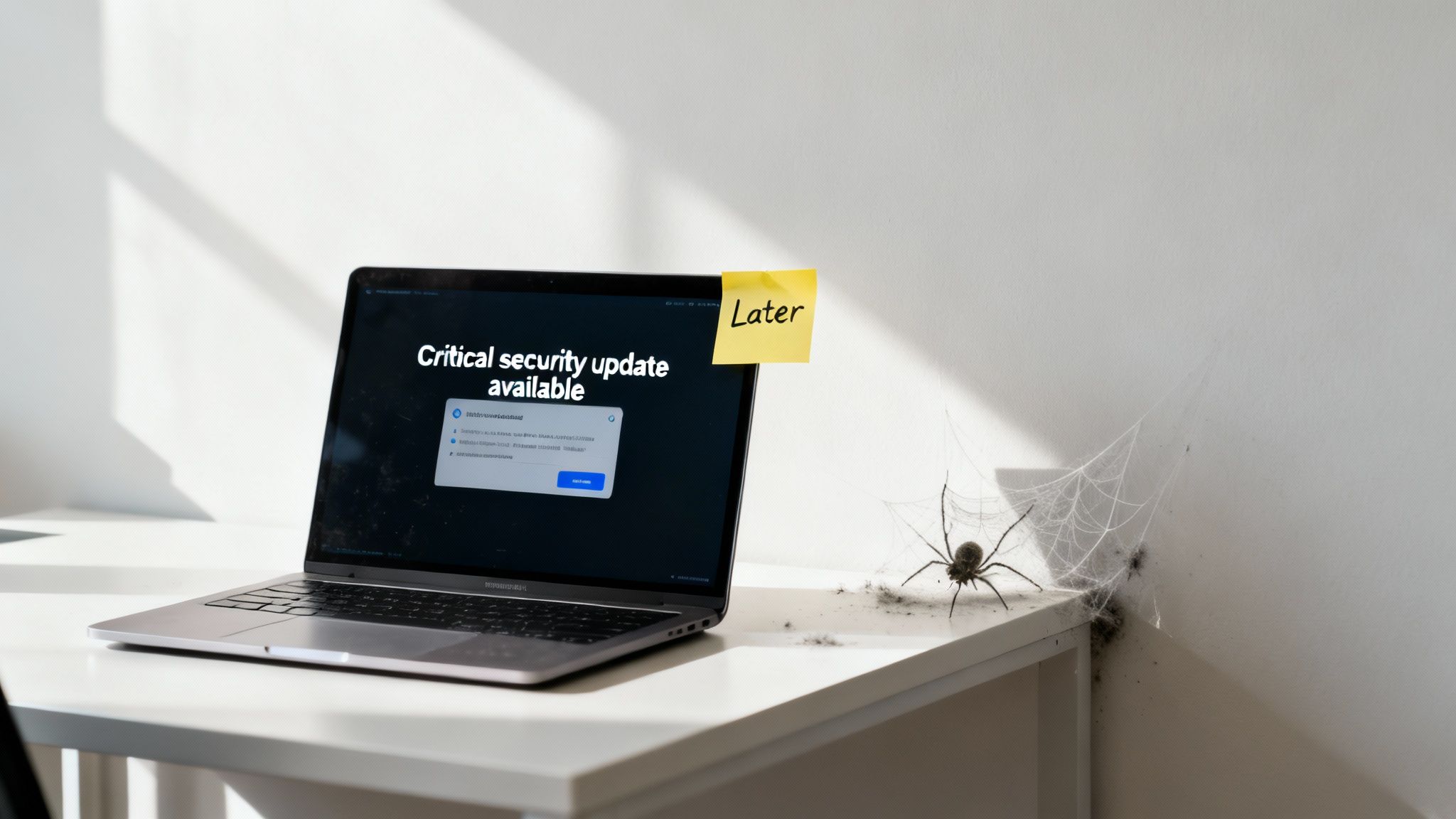
5. Myth #5: “Security Updates and Patching Can Wait”
It's easy to see a software update message and think, “I’ll do it later.” Many business owners put off these updates, thinking they are not important. This is a very risky idea. Delaying security updates, or "patches," is like leaving your front door unlocked when you know there are burglars in the area.
The idea that patching can wait is a dangerous myth because hackers don't wait. They use tools that constantly scan the internet for specific security holes, whether it’s on a Salinas Valley farm's network or a giant bank's. For them, a system that hasn't been updated is an open invitation.
Why Putting Off Patches is a Huge Risk
Hackers love old software because it gives them a reliable way into your network. Once a security hole is known, criminals rush to use it before businesses can apply the fix. They know that small businesses are often slow to update, making them easy targets. The reasons to update right away are clear:
- Automatic Attacks: Hackers use scanners to find vulnerable systems automatically. Your business isn't personally targeted; it's just caught in a big net.
- Known Weaknesses: Once an update is released, the security hole becomes public knowledge. Hackers then create tools to take advantage of that weakness.
- Big Consequences: A single missing update can lead to a ransomware attack, data theft, or a complete shutdown of your systems. The huge WannaCry attack in 2017 mostly hurt businesses that had failed to apply a simple Windows update.
- Rule Violations: Many industry rules require you to keep your software updated. Failing to do so can lead to big fines.
“An unpatched system isn't a future problem; it's a ticking clock. Cybercriminals are actively looking for that exact weakness, and they are counting on you to wait.”
The Data Doesn't Lie
The numbers show how dangerous delayed updates are. A Verizon report found that 60% of data breaches happened because of a known security hole that had a patch available. Most of the time, hackers are not using secret, advanced tricks; they are using old keys to open unlocked doors.
Recent security flaws in Microsoft Exchange and Apache Log4j showed how fast criminals can act, hitting hundreds of thousands of businesses in just a few weeks. The longer a system goes without an update, the more likely it is to be hacked. A plan for managing updates is not just good IT practice; it’s a basic business defense. To get started, you can learn more about the essentials of a strong patch management plan on adaptiveis.net.
5 IT Myths: Small Business Risk Comparison
| Item | Implementation complexity 🔄 | Resource requirements ⚡ | Expected outcomes ⭐ | Results / Impact 📊 | Key insights / tips 💡 |
|---|---|---|---|---|---|
| Small Businesses Are Too Insignificant to Be Targeted by Cybercriminals | Moderate — policy, MFA, backups, training required | Low–Medium — basic tools or MSSP support | Significant (⭐⭐⭐) — lowers likelihood & impact | Reduces targeted attacks, supply‑chain entry, recovery costs | Prioritize MFA, employee training, offline backups |
| Having a Firewall or Antivirus Is Sufficient Security Protection | Low to deploy but insufficient as sole control | Low — affordable baseline; needs EDR/SIEM to be effective | Limited (⭐) — blocks known/malware signatures only | Advanced threats, phishing, zero‑days often bypass these tools | Adopt defense‑in‑depth: EDR, segmentation, phishing training |
| Data Breaches Won't Impact Business Operations If They're Not Publicized | High — continuous monitoring, IR plan and testing needed | Medium–High — SIEM/SOC, forensic/legal support, notification processes | High (⭐⭐⭐) — early detection limits damage & fines | Undetected breaches increase costs, fines, downtime, reputational loss | Implement SIEM, incident response plan, tabletop exercises |
| Your Data Isn't Valuable Enough for Attackers to Target | Low–Medium — data inventory and classification work | Low–Medium — DLP, encryption, access controls, monitoring | Meaningful (⭐⭐) — limits monetization & credential misuse | Prevents resale/fraud, reduces lateral attack risk | Classify data, encrypt, restrict access, enable audit logging |
| Security Updates and Patching Can Wait; It Won't Affect Small Businesses | Moderate — formal patch management and testing required | Low — tooling + staff time; automation reduces burden | Very high (⭐⭐⭐⭐) — blocks most common exploit vectors | Significantly reduces exposure; prevents mass compromise | Automate patches, prioritize critical fixes, keep backups |
Move from Myth to Action: Secure Your Business's Future
Running a business in the Monterey Bay area is demanding. It’s easy to see why myths like "I'm too small to be hacked" start. But as we've shown, these ideas are not just wrong—they are dangerous. Believing your size makes you safe, that basic antivirus is enough, or that your data isn’t valuable are gambles that local businesses can no longer afford to take.
The truth is, hackers often prefer smaller targets because they know they are less protected. For them, it’s a numbers game, and businesses in Salinas, Monterey, and our local communities are all part of it. The question is no longer if you will be targeted, but when and how ready you will be.
Your Path Forward: From Awareness to Action
Understanding these myths is the first step. The next is to turn that knowledge into a real security plan. Protecting your business doesn't require a huge budget or your own IT department. It’s about building smart, affordable defenses that grow with your company.
Here are the key takeaways for your action plan:
- Know Your Value: Every business has valuable data. Customer lists, financial records, and employee information are all assets. Treat your data security seriously.
- Use Layered Security: One tool is never enough. Your defense should be a system that includes a strong firewall, good antivirus, regular software updates, employee training, and secure passwords.
- Be Proactive: Don’t wait for something to break. Regular security updates are one of the best and most affordable ways to close the doors that hackers use to get in.
- Plan for the Worst: An attack can stop your business, hurt your reputation, and cost you a lot of money. As you take action, think about creating a plan for what to do if the worst happens. Looking at a business continuity plan example specifically for SMBs can give you a clear roadmap for how to prepare and recover quickly.
The journey from thinking “you’re too small to be hacked” to building a secure, strong business is one of the most important investments you can make. It’s about more than technology; it’s about protecting the future of the business you’ve worked so hard to build.
If you're a local business owner in Salinas, Monterey, or nearby who’s unsure whether you need IT support—let’s talk. Adaptive Information Systems offers friendly consultations and tailored tech plans that make sense for your size, industry, and goals. We specialize in breaking down complex IT topics into clear, local solutions.
Adaptive Information Systems
380 Main St, Salinas CA 93901 | 831-644-0300 | hello@adaptiveis.net