As a business owner in Monterey County, you're constantly juggling budgets. It’s easy to look at cybersecurity and see just another expense you might be tempted to cut. But what's the real cost of skipping security? The hard truth is that any money you "save" upfront is pocket change compared to the huge costs of cleaning up after a data breach. For businesses here in Salinas, ignoring security is a gamble you can't afford to take.
More Than Just an Expense—It’s an Investment
When you’re running a business, every dollar counts. So, the question, “Isn’t cybersecurity out of our budget?” is completely understandable. However, recent insights show that 80% of SMBs are increasing cybersecurity budgets in 2025, recognizing the rising risks and the long-term savings of proactive protection.
Think of security less like an expense and more like the insurance you have on your building or work trucks. It’s a key investment in protecting the digital foundation your entire business is built on. Proactive security isn't a luxury; it's a core part of your survival plan.
This isn't just a big-city problem anymore. Your local competitors right here in Carmel and Seaside are making security a priority, especially those in Monterey County's vital industries like agriculture and hospitality. Ignoring this shift puts your business at a serious, and completely avoidable, disadvantage.
A Clear Shift in Business Priorities
The numbers don't lie. A massive 80% of small and medium-sized businesses (SMBs) are actively increasing their cybersecurity budgets. They're not doing it because they have extra cash lying around; they're doing it because they understand the rising risks and the long-term savings of proactive protection.
They’ve done the math and realized the cost of recovery is much, much higher than the price of prevention.
What this actually means for you is that security doesn’t have to break the bank. You don’t need the same fortress-like setup as a massive corporation. Scalable solutions like managed firewalls, MFA, and employee training can be customized to fit your size and risk profile.
Modern cybersecurity is all about smart, targeted protection that fits your specific business.
Making Security Affordable and Actionable
The key is to start with the essentials. Just like you lock your doors at night, there are basic digital locks every business needs. In fact, many of the cyber threats no one warns small businesses about can be stopped with simple, affordable tools.
A great first step is a cybersecurity essentials package. Adaptive offers entry-level protection bundles designed specifically for small businesses in Salinas and Monterey. These packages form the core of a strong defense and connect directly with your IT Infrastructure Management to make sure your whole operation is secure.
At-a-Glance Breach Recovery vs Proactive Security Costs
This table provides a quick comparison to show the big financial difference between investing in basic security and recovering from a single incident.
| Cost Area | Reactive Cost After a Breach | Proactive Investment |
|---|---|---|
| Downtime & Lost Revenue | $5,000 – $50,000+ per day | $0 (systems remain online) |
| Forensic Investigation | $10,000 – $25,000+ | Included in managed services |
| Legal Fees & Fines | $5,000 – $100,000+ | Minimized by compliance measures |
| Reputation Damage | Incalculable (long-term loss of trust) | Strengthened client confidence |
| Data Recovery | $2,000 – $15,000 | Covered by robust backup systems |
| Total (Single Incident) | Potentially $22,000 – $190,000+ | A fraction of the cost, paid monthly |
The contrast is clear. A proactive approach turns a potentially catastrophic disaster into a predictable, manageable operating expense.
Wondering what cybersecurity your business actually needs? Let’s assess your risk and build a plan that fits your budget—start with a free consultation.
Adaptive Information Systems
380 Main St, Salinas CA 93901 | 831-644-0300 | hello@adaptiveis.net
Deconstructing the Financial Fallout of a Breach
When a data breach hits, the damage is never just one bill. It’s a cascade of costs that can quickly overwhelm a small business. For many local businesses in Salinas, the aftermath can feel just as devastating as an equipment failure on the farm or an unexpected shutdown during peak tourist season in Monterey.
The first shockwave hits your bank account almost immediately. These are the direct, hard costs you have to pay out of pocket, right now. Think of it as the emergency room bill for your business—it's urgent, expensive, and just the beginning.
The Immediate, Hard Costs You Can Expect
The moment a breach is confirmed, the clock starts ticking, and so does the meter on expenses. These aren't abstract concepts; they are real invoices that will land on your desk.
- Forensic Investigation: You'll need to hire experts to figure out how the breach happened, what data was taken, and how to stop the bleeding. This is a non-negotiable first step, and it can easily cost tens of thousands of dollars.
- Business Disruption: Every minute your systems are down, you're losing money. You can't process payments, access customer records, or manage your inventory. This operational paralysis is a direct hit to your revenue stream.
- Data Recovery: Getting your data back comes with a hefty price tag, whether you're restoring from backups or—in the worst-case scenario—dealing with a ransomware attack.
This visual breaks down the stark contrast between a small, proactive investment in security and the massive, reactive cost of cleaning up a breach.
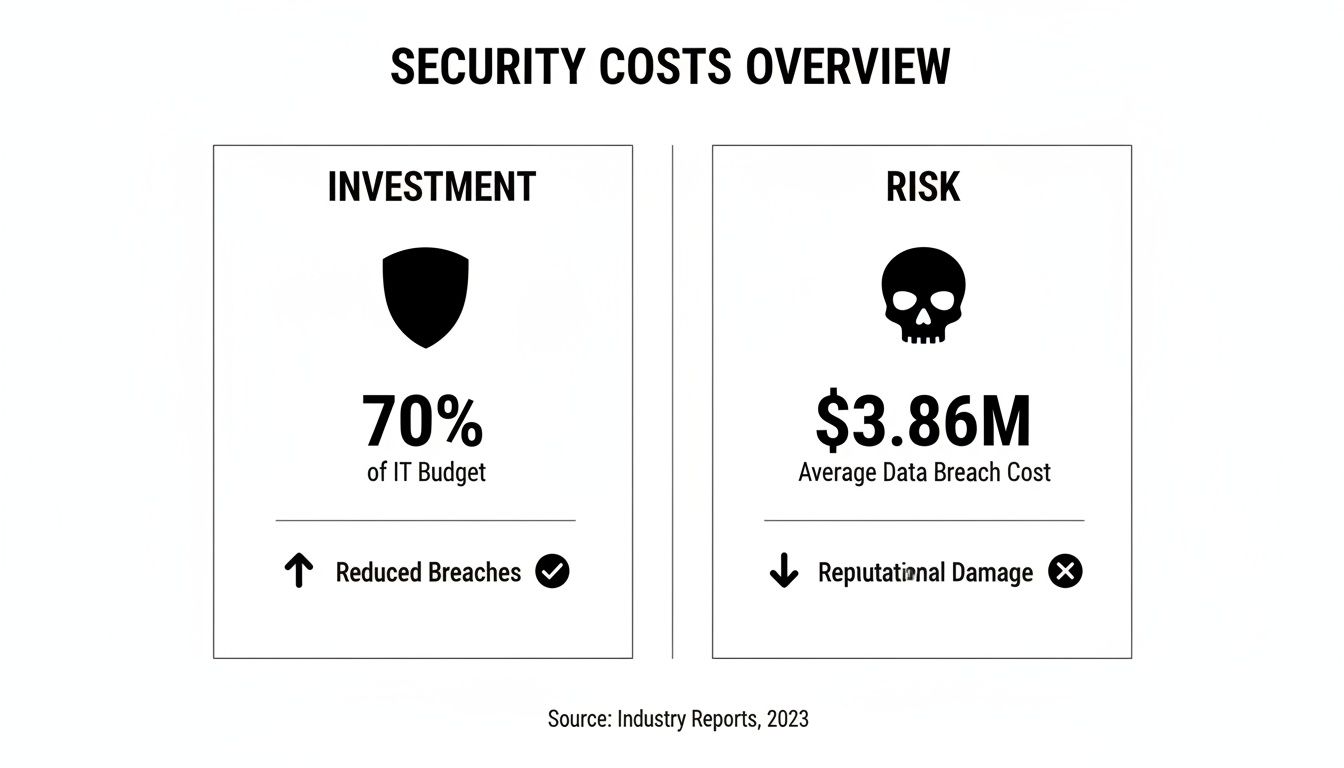
As you can see, the expenses that pile up after a breach dwarf the manageable costs of foundational security.
Long-Term Financial Bleeding and Regulatory Fines
Beyond the initial cleanup, a breach creates long-term financial costs that can linger for months, if not years. These costs are often even more significant than the immediate response.
The numbers are staggering. According to IBM's latest research, the global average cost of a data breach has hit $4.45 million. For U.S. companies right here in California, that number skyrockets to a record-breaking $9.48 million. This isn't just a big-corporation problem, either; small and mid-sized businesses saw their average breach costs climb to $3.31 million.
This long-term financial fallout includes several key areas:
- Regulatory Fines: If your business handles sensitive information like credit card data (PCI DSS) or health records (HIPAA), you're on the hook for major fines. To get a real sense of the financial penalties, it's vital to understand the consequences of PCI non-compliance.
- Legal Fees: It’s common to face lawsuits from customers whose data was compromised. This leads to significant legal defense costs and potentially crippling settlements.
- Customer Notification and Credit Monitoring: You are legally required to notify every individual affected. It’s also standard practice to offer them free credit monitoring services—an expense that adds up quickly.
- Increased Insurance Premiums: After a breach, your cyber liability insurance premiums will almost certainly go up, adding a recurring expense to your budget for years to come.
When you add it all up, the financial fallout from a single security lapse can easily eclipse what you would have spent on years of professional, managed security.
How Downtime and Disruption Grind Your Business to a Halt
Financial penalties are just one piece of the puzzle. The most immediate and painful consequence of a cyberattack is often the simplest one: your business just stops working. This is where the real cost of skipping security becomes painfully clear, grinding your entire operation to a halt.
Imagine this: It's a busy Tuesday at your hospitality business in Pacific Grove. Suddenly, your reservation system goes dark. You can't check guests in, process payments, or even see who's supposed to arrive. Your team is left scrambling with pen and paper while frustrated customers wait. This isn't just an inconvenience; it's a direct, hour-by-hour loss of revenue and reputation.

This kind of disruption cascades through every part of your business, creating a ripple effect of chaos and lost productivity.
The True Price of Lost Time
Every hour your systems are down is an hour you aren't serving customers or billing for services. For our agricultural clients in the Salinas Valley, downtime during planting or harvest season can be catastrophic, disrupting supply chain commitments.
The clock is ticking from the moment an attack hits, and the costs multiply quickly.
- Lost Revenue: This is the most obvious cost. If your point-of-sale system is down or your e-commerce site is offline, you are making $0 in sales.
- Employee Productivity tanks: Your team can't access their tools or client files. You're paying your staff to wait, unable to do their jobs.
- Supply Chain Chaos: You can't place orders with vendors or fulfill orders for your customers. This leads to broken commitments and damaged relationships.
- Missed Opportunities: While you're busy putting out fires, your competitors are busy serving your customers. Every new lead or sales call you miss is a potential long-term loss.
This period of forced inactivity isn't short. Recovering from a significant breach is often a matter of days or even weeks of painstaking work.
Recovery Is a Marathon, Not a Sprint
The time it takes to contain and recover from a breach has a direct and massive impact on the total cost. Recent data from IBM highlights this starkly: breaches that take longer than 200 days to contain cost an average of $1.02 million more than incidents contained within that timeframe.
When you factor in the average cost per compromised record and the staggering expense of lost business, which averages $1.38 million, you can see how a slow recovery can be fatal for a small business.
A cyberattack forces you to stop working on your business and start working on a disaster. Your focus shifts from growth to damage control.
This is precisely why a proactive defense is so critical. A stable, secure foundation is the best insurance against catastrophic downtime. Having a clear recovery strategy is essential, which is why we created a business continuity plan checklist to help you prepare before an incident occurs. Proactive planning transforms a potential catastrophe into a manageable event.
Why Human Error Is Your Hidden Vulnerability
When you think about cyber threats, you might picture a shadowy hacker in a dark room. While external attacks are a real danger, one of the biggest security risks is much closer to home. The truth is, many breaches begin right inside your office, often with a simple mistake.
This is the hidden vulnerability of human error, and it’s a critical part of understanding the real cost of skipping security. Your team is your greatest asset, but without the right training, they can accidentally become your weakest link. It’s not about blame; it’s about recognizing that busy, well-intentioned employees are the primary targets for cybercriminals.

Everyday Scenarios That Open the Door
These are everyday situations that happen in businesses across Monterey County, from hospitality to agriculture.
- The Convincing Phishing Email: A team member gets an urgent email that looks like it’s from a trusted vendor asking them to click a link to view an invoice. In a rush, they click, and malware is now on your network.
- The Unsecured Access: A former employee who left on good terms still has access to your company’s cloud storage. That old account becomes a forgotten, unsecured entry point.
- The Weak Password: An employee uses a simple password like "Salinas123" for multiple work accounts. Once a criminal cracks that one password, they have the keys to your sensitive company data.
These seemingly small slips are precisely what cybercriminals count on. They know that targeting your people is often far easier than trying to smash through a firewall.
The Staggering Cost of Insider Threats
While often accidental, these internal incidents can be incredibly damaging. The financial fallout from a breach caused by a phishing scam can be devastating for a small business.
Recent data from IBM's breach report highlights that malicious insider attacks are the costliest of all, averaging a shocking $4.90 million per incident. Phishing, which played a role in 16% of breaches, wasn't far behind, with an average cost of $4.76 million. Critically, the report found that organizations lacking security skills and employee training faced significantly higher breach costs. You can read more about these findings on the high cost of data breaches.
For a local business, a multi-million-dollar price tag isn't just a setback; it's a business-ending event. This is why investing in your team’s security awareness isn’t just a "nice-to-have"—it's a core financial defense strategy.
Turning Your Team into Your First Line of Defense
The good news is that tackling the risk of human error is one of the most affordable and high-impact security measures you can take. It’s not about buying complex software; it’s about building a security-conscious culture.
Great security is a combination of smart technology and smart habits. By focusing on a few key areas, you empower your employees to become your first line of defense.
You can start by evaluating your current practices with a comprehensive cybersecurity audit checklist to identify where your most significant human-related risks are. From there, you can implement simple yet powerful tools to lock down your business from the inside out. This proactive approach strengthens your entire security posture.
The Reputational Damage That Money Cannot Fix
You can put a price on downtime and calculate the cost of fines, but some consequences of a security breach never show up on a spreadsheet. We’re talking about the one asset you’ve worked hardest to build: your customers’ trust. This is where the real cost of skipping security hits home, leaving a long-term stain on your reputation.
Financial losses sting, but they can often be covered by insurance or earned back over time. A shattered reputation is a different kind of wound. It bleeds customer loyalty, poisons your brand, and makes attracting new clients incredibly difficult.

When Trust Walks Out the Door
Imagine you’re a trusted financial advisor in Carmel. For years, clients have given you their most sensitive personal details. Now, picture having to call each one to say that all of that data is in the hands of criminals.
Or think about your popular Monterey restaurant after a breach exposes every credit card number swiped over the last six months. That news would spread like wildfire through our tight-knit local community. Overnight, you’re no longer known for your amazing food, but for being "that place that got hacked."
The moment you lose a customer's trust, you don't just lose their next transaction. You lose their lifetime value and their positive word-of-mouth—the lifeblood of a local business.
This kind of customer churn isn't a slow leak; it’s a flood. Clients will quickly flock to competitors they see as safer, and winning them back is a monumental task.
The Long Shadow on Your Brand
The fallout doesn't stop with your current customers. A security breach casts a long, dark shadow that can jeopardize your brand’s future.
Here’s what that lasting damage looks like:
- Difficulty Attracting New Clients: The first thing potential customers do is search for you online. If the top results are news articles about your data breach, they’ll almost certainly go elsewhere.
- Struggles with Hiring: Top talent wants to work for stable, reputable companies. A public security failure makes potential employees question your management.
- Damaged Partner Relationships: Suddenly, your vendors are hesitant to connect their systems with yours. They worry that your security weaknesses could put them at risk, too.
In the end, this emotional and relational cost is often the most powerful reason to get serious about proactive security. Protecting your data isn't just about technology; it's about honoring the trust your customers and community have placed in you.
Making Smart Cybersecurity Affordable and Actionable
After seeing the numbers, it’s natural to ask: “Isn’t real cybersecurity just for big corporations?” This is one of the first things we hear from business owners in Salinas, and it's a valid concern.
The good news? Protecting your business is far more affordable than you might think.
The goal isn't to build an impenetrable fortress. It’s about putting smart, practical defenses in place that give you the most bang for your buck. You can get serious protection without paying an enterprise-level price tag.
Shifting from Expense to Investment
The myth that solid security is too expensive is quickly falling apart. As mentioned, 80% of small and medium-sized businesses (SMBs) are increasing their cybersecurity budgets because they know preventing a disaster is profoundly cheaper than cleaning one up.
What this really means is that modern security is built to scale. It can be tailored to fit your company’s size, your industry's risks, and your actual budget. By focusing on the fundamentals first, you build a strong foundation that knocks out the most common threats without wasting money.
This strategic approach turns cybersecurity from a daunting cost into a predictable part of your operational plan, directly protecting your bottom line.
Your First Steps to Affordable Cybersecurity
Getting started is simpler than you might imagine. Just a few foundational security measures can neutralize a huge percentage of the threats targeting businesses today. For a deeper dive into budget-friendly options, you can explore resources that cover affordable cybersecurity services tailored for small and medium businesses.
Here’s a look at the core components that form the basis of any strong, cost-effective defense.
| Security Measure | What It Protects Against | Typical Investment Level |
|---|---|---|
| Managed Firewall | Unauthorized network access, malware, and intrusion attempts. | Low |
| Multi-Factor Authentication (MFA) | Compromised passwords and unauthorized account access. | Very Low |
| Employee Security Training | Phishing scams, social engineering, and accidental data leaks. | Low |
| Managed Backups | Data loss from ransomware, hardware failure, or human error. | Low to Medium |
These elements aren't standalone solutions; they work together to create layers of protection. A firewall acts as your digital gatekeeper, MFA secures your accounts even if a password is stolen, and training empowers your team to spot threats.
If you’re feeling overwhelmed, you are not alone. Our guide on how outsourced cybersecurity is reshaping small business IT can show you how a partner can simplify this entire process.
Wondering what cybersecurity your business actually needs? Let’s assess your risk and build a plan that fits your budget—start with a free consultation.
Adaptive Information Systems
380 Main St, Salinas CA 93901 | 831-644-0300 | hello@adaptiveis.net
Got Questions About SMB Cybersecurity? So Does Everyone Else.
Even after laying out all the facts, it’s natural to have a few questions. Let's tackle some of the most common ones we hear from business owners right here in the Monterey Bay area.
"Honestly, Isn't My Business Too Small to Be a Target?"
This is probably the most dangerous assumption a small business owner can make. The thinking goes that hackers are only interested in the big fish. But that’s not how modern cybercrime works.
Automated attack bots don't care if you're a Fortune 500 company or a local flower shop. They just scan the internet for vulnerabilities—an open digital door. In fact, cybercriminals often see smaller businesses as easier targets because they bet you haven't invested in security. You're not a name on a list; you're just an easy payday.
"Okay, but My Budget Is Tight. What's the Single Most Important First Step?"
If you have to start somewhere, focus on the two biggest bangs for your buck: Multi-Factor Authentication (MFA) and regular employee security training. These aren't flashy or expensive, but they are incredibly effective.
Why these two? Because they directly shut down the most common ways criminals get in—stolen passwords and human error. Setting up MFA is often free, and a simple training session can turn your team from a liability into your first line of defense. It's the biggest risk reduction you can get for the smallest investment.
The real cost of skipping security isn't just about losing money; it's about losing the trust you've worked so hard to build with your customers and community.
"How Long Does It Take to Get Basic Protection in Place? Is This Going to Disrupt Everything?"
It’s much faster and less painful than you probably imagine. We're not talking about weeks of downtime.
Foundational pieces like a managed firewall or rolling out MFA can be handled by a professional IT team with almost no interruption to your day-to-day work. A team like Adaptive manages the whole process, getting your business protected quickly and correctly so you can keep your focus where it belongs: on running your business.
Wondering what cybersecurity your business actually needs? Let’s assess your risk and build a plan that fits your budget. The team at Adaptive Information Systems is here to help.
Start with a free consultation today by visiting https://adaptiveis.net.
Adaptive Information Systems
380 Main St, Salinas CA 93901 | 831-644-0300 | hello@adaptiveis.net
