As a business owner in Salinas, you’ve probably asked yourself a common question: “Isn’t antivirus enough to keep us protected?” For a long time, the answer was yes. But today, if you’re still relying only on antivirus software, you’re leaving your business dangerously exposed. Recent insights show that 80% of small businesses are boosting their cybersecurity budgets in 2025, indicating antivirus alone no longer cuts it.
The simple answer today is that antivirus isn’t enough anymore. While it's still an essential piece of the puzzle, it can no longer protect your business on its own against modern cyber threats.
Why Your Antivirus Is No Longer Enough

Think of your antivirus software as a sturdy padlock on your office’s front door. It’s a good first line of defense, designed to stop known troublemakers from walking right in. But what happens when criminals don’t even bother with the front door? Today’s hackers are much smarter, targeting your business from every possible angle.
This is why recent insights show that 80% of small businesses are boosting their cybersecurity budgets in 2025. Your peers in Monterey County and across the country see that the game has changed. To be truly protected, it's clear that essential security solutions for businesses must go far beyond a single defense like antivirus.
Hackers Have Evolved Their Tactics
What this actually means for you is that hackers have evolved—ransomware, phishing, and network breaches require multi-layered defenses. These modern threats bypass that front-door lock by finding other ways in.
Let's take a quick look at what your antivirus was designed for versus the complex attacks it now faces.
Old Threats vs Modern Threats
| Threat Type | Antivirus Effectiveness | Modern Defense Needed |
|---|---|---|
| Known Viruses & Malware | High – This is its core job. | Still needs antivirus, but it's just one layer. |
| Phishing Emails | Low – Can't stop an employee from clicking a link. | Advanced email filtering, employee training. |
| Ransomware | Very Low – Often uses fileless techniques to avoid detection. | Endpoint Detection & Response (EDR), backups. |
| Zero-Day Attacks | None – By definition, the threat is unknown. | Proactive monitoring (SOC), EDR/XDR solutions. |
| Fileless Attacks | None – No malicious file to scan. | Behavioral analysis, 24/7 monitoring. |
As you can see, the attacks that cause the most damage today are the ones that sidestep traditional defenses entirely. They don't use the front door; they come through other weak spots:
- The Windows (Phishing): Tricking an employee into clicking a malicious link in an email is like convincing them to open a window for a burglar.
- The Back Door (Ransomware): This type of attack sneaks in and encrypts all your critical files, effectively locking you out of your own business until you pay a hefty fee.
- The Wi-Fi (Network Breaches): An unsecured or poorly configured network connection can be an open invitation for intruders to gain access to your entire system.
Antivirus is just the front door lock, but today’s threats come through the windows, Wi-Fi, and employee inboxes too. You need a complete security system to protect the whole building.
Upgrading to a Layered Defense
The solution isn't to get rid of your antivirus but to build smarter, stronger defenses around it. You need a modern, layered security strategy that covers all potential entry points, not just one. This includes things like a firewall, 24/7 monitoring, compliance tools, and user training.
At Adaptive, we specialize in creating these multi-layered security strategies for SMBs, tailored to the unique risks facing local industries like agriculture and hospitality. We’ll help you understand how cyber threats are evolving and build an affordable defense that lets you focus on your business with real peace of mind. Adaptive offers SMB-friendly bundles tailored to your risk profile.
How Cyber Threats Evolved Beyond Viruses
To really get why your old security setup is failing, you have to understand just how much the bad guys have leveled up. Today's cybercriminals aren't like the digital burglars of the past; they're more like sophisticated engineers, designing attacks that waltz right past traditional antivirus.
Antivirus software was built for a simpler time. Its entire job was to act like a security guard with a photo album of known criminals. If it saw a piece of software that matched a photo in its database, it sounded the alarm.
The problem? Modern attacks don't have a photo on file.
The Rise of Ransomware
Picture this: a hacker slips into your network, but instead of quietly stealing data, they lock up everything. Your client records, financial documents, operational files—all encrypted and completely inaccessible. This is ransomware, and it can bring your Pacific Grove hospitality business or Salinas ag-tech firm to a dead stop overnight.
Because these attacks often use your computer's own legitimate tools to do their dirty work, traditional antivirus frequently doesn't see a problem until it's far too late. The attackers then hit you with a massive ransom demand to get your data back, leaving you with a truly impossible choice.
Exploiting Your Team with Phishing
Your biggest security weak point isn't a piece of software; it's the people on your team. Phishing and social engineering attacks don't hack computers—they hack human trust. A cleverly disguised email that looks like it's from a trusted vendor can trick an employee into revealing their password or downloading a file that opens the floodgates.
Antivirus can't stop a person from clicking a convincing link. These attacks turn your own staff into unwitting accomplices, handing hackers a key to your most sensitive information. You can learn more about these tactics in our guide on the cyber threats no one warns small businesses about.
The Danger of Invisible Attacks
Some of the most dangerous modern threats are the ones antivirus software can't even see in the first place.
- Fileless Attacks: These nasty threats operate entirely in your computer’s memory (RAM). They never write a malicious file to the hard drive, which means there's literally no file for your antivirus to scan. It's completely blind.
- Zero-Day Exploits: These attacks target brand-new, undiscovered vulnerabilities in the software you use every day. Since the vulnerability is unknown to the software developer, there’s no "signature" or "photo" for an antivirus program to look for.
This is the new reality. Relying only on antivirus is like trying to stop a flood with a single sandbag—the water will always find a way around it.
Recent data shows just how big this gap is. Even with high antivirus adoption, a staggering 36% of users still get infected. This failure against modern threats like ransomware and encrypted attacks is exactly why businesses need more advanced defenses. Today’s threats demand a multi-layered security strategy that sees what old-school antivirus misses.
Building Your Modern Security Stack
Alright, you get it—the old ways aren't cutting it anymore. So, what’s the right way to protect your business? The answer isn't just to toss your old antivirus software in the trash. Instead, it’s time to build smarter, stronger walls around it, creating layers of defense that actually work together.
This layered strategy is what we in the industry call a "security stack."
Think about securing your office building. You wouldn't rely on just the lock on the front door, right? You’d want sturdy walls, maybe some security cameras, controlled access to the server room, and an offsite safe for your most critical documents. Your digital security should be built the same way—with multiple layers that back each other up.
The flowchart below gives you a quick visual of why a single tool just doesn't work against the variety of threats we see today.
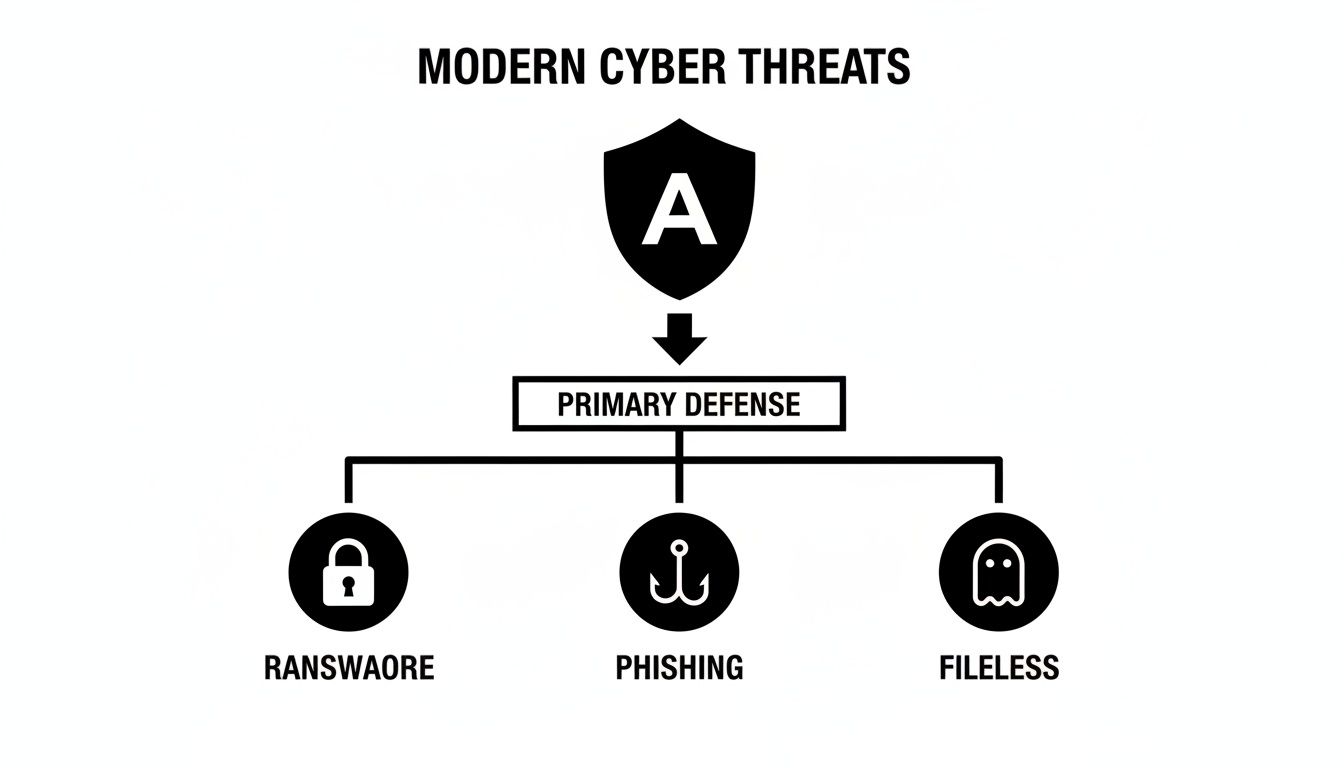
As you can see, antivirus is just one piece of the puzzle, facing a whole lineup of sophisticated attacks that require their own specialized defenses.
Core Layers of Modern Defense
So, what do these layers look like in the real world? A strong security stack is made up of a few key components, each designed to protect you from a different angle. If one layer gets breached, another is already in place to stop the attack in its tracks.
Here are the absolute essentials you need to have:
- Endpoint Detection and Response (EDR): This is the evolution of antivirus. Instead of just looking for known virus files, EDR actively hunts for suspicious behavior on your computers and servers. Think of it less like a bouncer with a list of known troublemakers and more like a security guard who spots someone acting strangely and intervenes before they can cause a problem.
- Advanced Email Security: With so many attacks starting from a simple phishing email, you need a powerful filter that can spot and block malicious messages before they ever land in your team's inboxes. This layer is the gatekeeper for your most-used communication tool.
- Employee Security Training: At the end of the day, your team is your first and last line of defense. Consistent training turns them from a potential vulnerability into a powerful security asset by teaching them how to spot phishing attempts and other social engineering tricks.
The Foundational Security Tools
Beyond those active hunting and training layers, your security stack needs a rock-solid foundation. These are the tools that work quietly in the background, 24/7, to control access and make sure you can get back on your feet quickly if an incident does happen.
A complete security strategy protects your data, your people, and your operations. It’s about building a system where every piece works together to keep your business safe and running smoothly.
This means putting up a robust firewall to act as your network's perimeter and enforcing Multi-Factor Authentication (MFA), which requires a second code or tap to verify an identity before granting access.
And, of course, you need a bulletproof Backup and Disaster Recovery plan. This is your ultimate safety net. If the worst-case scenario happens, you can restore your data and get back to business—without ever having to consider paying a ransom.
This might all sound complex, but our mission at Adaptive is to make enterprise-level IT accessible and affordable for local SMBs. You can explore some of our cybersecurity solutions for small business to see exactly how we build these layers for companies just like yours. A modern security stack isn't a luxury anymore; it's a necessity, and we make it achievable.
Your Layered Security Checklist
To put it all together, think of your security stack as a checklist. Each layer addresses a specific type of threat, and having them all in place gives you a comprehensive defense.
| Security Layer | What It Does | Threat It Stops |
|---|---|---|
| EDR / XDR | Actively monitors endpoint and network behavior for threats. | Fileless Attacks, Zero-Days, Ransomware |
| Email Security | Filters incoming emails for malicious links, attachments, and scams. | Phishing, Business Email Compromise |
| MFA | Requires a second form of verification to access accounts. | Stolen Passwords, Unauthorized Access |
| Backups & Recovery | Creates copies of your data to restore in case of an incident. | Ransomware, Data Loss, Hardware Failure |
| Security Training | Educates employees to recognize and report threats. | Social Engineering, Phishing |
With these layers in place, you move from a reactive, hope-for-the-best approach to a proactive, resilient security posture that can stand up to modern threats.
Why 24/7 Monitoring Is a Game Changer for SMBs

Many business owners in Marina and Seaside still believe that serious cybersecurity is just for big corporations with bottomless budgets. This is probably one of the most dangerous myths in IT today, especially when it comes to a security layer that’s absolutely critical: 24/7 monitoring.
The hard truth is that cyberattacks don’t clock out at 5 p.m. A threat can pop up on a Friday night or a holiday weekend when your entire team is offline. Without someone watching, a minor security alert can snowball into a full-blown crisis by the time you walk in on Monday morning.
This is where a managed service provider like Adaptive becomes your dedicated, round-the-clock security team. We watch over your network constantly, making sure threats are spotted and shut down in real-time, no matter when they decide to strike.
Proactive Defense Instead of Costly Reaction
Traditional antivirus is purely reactive. It only kicks into gear when it recognizes a known piece of malware trying to get in the door.
Modern network security monitoring, on the other hand, is proactive. It looks for any unusual activity—like a login from an unexpected country or a computer suddenly trying to access sensitive files—and investigates it immediately.
This proactive approach stops problems like data breaches and expensive downtime before they can actually hurt your business. It's the difference between having a smoke detector that goes off at the first hint of trouble versus discovering the fire after half the building is already engulfed in flames.
Staying Ahead of Invisible Threats
The numbers tell a pretty stark story. In 2025, antivirus software is expected to detect over 560,000 new malware instances every single day. The bigger problem? A staggering 60% of them hide inside encrypted traffic, where basic tools simply can't see them.
With confidence in antivirus dropping fast—only 25% of users now consider it 'very effective'—it’s obvious that we need more than just a digital gatekeeper. We need active threat hunting to cover the gaps. You can discover more antivirus statistics and trends on Impulsec.com to see just how big the problem has become.
Having a team actively monitoring your network is like having security guards patrolling your property 24/7. They don't just wait for an alarm to go off; they actively look for signs of trouble and stop intruders before they ever get inside.
This constant vigilance is a complete game changer. It means you can focus on running your business, confident that experts are always watching your back.
Meeting Compliance and Protecting Your Reputation
For many local industries in Monterey County, from healthcare to finance, this level of security isn't just a good idea—it's a requirement. Regulations like HIPAA or CMMC demand robust and continuous security monitoring to protect sensitive client and patient data.
Failing to meet these standards can lead to crippling fines and a loss of client trust that can be nearly impossible to win back. By partnering with a managed provider for 24/7 monitoring, you not only get superior protection but also the documentation and processes you need to prove your business is both compliant and secure.
Integrating VoIP Security Into Your Defense
Your phone system is the lifeblood of your business. It’s how you connect with clients, coordinate with vendors, and keep your own team in sync. But as businesses have shifted away from old copper phone lines to modern Voice over IP (VoIP), phones have become just another device on the computer network—and that makes them a target.
This is a perfect example of why antivirus isn’t enough anymore. Your security strategy has to cover every single device connected to your network, and that absolutely includes your phones. VoIP security fits right into your overall security stack. If it’s not properly secured, it can become an open door for criminals looking for an easy way into your network.
Common Threats to Your Phone System
An unsecured VoIP system opens you up to some nasty risks that go far beyond a simple computer virus. Attackers have a few favorite ways to exploit them, and each one can be seriously disruptive.
- Call Interception: This is exactly what it sounds like. Hackers can eavesdrop on sensitive conversations, potentially grabbing confidential client details or listening in on internal strategy talks.
- Denial-of-Service (DoS) Attacks: An attacker can flood your phone system with so much junk traffic that it completely shuts down. Suddenly, neither you nor your customers can make or receive legitimate calls.
- Vishing (Voice Phishing): This one is especially sneaky. Criminals can hijack your caller ID to impersonate your business, then call your clients and trick them into giving up sensitive information like passwords or credit card numbers.
Protecting your VoIP system isn’t just an IT task; it’s about safeguarding your company's private conversations and its hard-earned reputation. A layered defense makes sure your phone lines are just as secure as your financial data.
Securing Your Communications Stack
So, how do you lock this down? It all starts with treating your phones as a core part of your security stack. The same principles that protect your computers apply here. A strong firewall, continuous network monitoring, and proper device configuration are your first and most important lines of defense.
When you’re weaving VoIP security into your overall strategy, you need a solid foundation. Looking into options like reliable VoIP phone systems for small businesses is a good starting point to understand what a secure, modern system looks like.
From there, we add specific layers of protection, like call encryption to prevent anyone from eavesdropping and strict access controls to ensure only authorized people can make changes to the system. This integrated approach closes the kind of security gaps that hackers absolutely love to find and exploit. At Adaptive, we help businesses understand all their options with our complete VoIP Solutions for small businesses, ensuring your communications are protected under one cohesive and affordable plan.
Time for a Reality Check
Realizing that your old antivirus software isn't cutting it anymore is a huge first step. It means you've moved past the outdated "set it and forget it" mindset. Now, it's time to build a real defense.
The big takeaway here is that security isn't about one magic-bullet product. It's a strategy. Think of it like locking up a physical store—you don't just lock the front door and call it a day. You have locks on the windows, a security camera system, and an alarm. A modern cybersecurity defense works the same way, with layers designed to protect you from different angles.
That might sound like a massive, expensive project, but it doesn't have to be. At Adaptive Information Systems, we build security packages specifically for small and mid-sized businesses right here in our community, from Salinas agriculture to Carmel hospitality. Our entire mission is to deliver the kind of robust IT security the big corporations have, but at a price that actually works for a local business budget.
See Your Own Risks Firsthand
It’s one thing for us to talk about fileless attacks and zero-day threats; it's another thing entirely to see exactly where your own business is exposed. A recent report from Security.org really drives this point home. While 66% of adults use some form of antivirus, a staggering 36% still get hit with infections.
Even more concerning is the false confidence people place in the free, built-in tools. Infection rates for pre-installed antivirus software are sitting at a shocking 42%. You can read the full antivirus consumer report on Security.org to see just how wide the gap is between perceived safety and actual protection.
To close that gap, we want to give you a clear, no-nonsense look at your own setup.
Want a real-world look at your current vulnerabilities? Get a free network risk scan today—no strings attached.
This isn't a sales pitch. It’s a complimentary, confidential report that shows you exactly where your current security stands. Think of it as a blueprint for your defense, giving you the hard data you need to make smart, informed decisions about protecting your company's future.
Taking this first step puts you back in the driver's seat. Let our team help you build a defense that lets you get back to what you do best—running your business with genuine peace of mind.
Have Questions? We Have Answers.
As a business owner, thinking about moving past a simple antivirus program can bring up a lot of practical questions. We get it. Here are the clear, direct answers to the most common concerns we hear from local businesses just like yours.
Isn't This Kind of Layered Security Expensive for a Small Business?
This is always the first question, and the answer is a straightforward no. Our entire mission at Adaptive is to make enterprise-level IT security genuinely affordable for local small and mid-sized businesses. A bundled, managed service is always far more cost-effective than trying to piece together separate solutions from ten different vendors.
But more importantly, the cost of proactive security is just a tiny fraction of what a single data breach would cost you. Think about the price of downtime, recovery fees, regulatory fines, and the damage to your hard-earned reputation. The math is pretty clear.
My Business Is Small. Are We Really a Target?
Yes, absolutely. In fact, hackers often see small businesses as the ideal targets because they assume you have fewer security resources than a big corporation. It's nothing personal.
They aren't necessarily after your business by name; they're after your data, your bank account, or your network access to one of your larger clients. A strong, layered defense makes you a much harder target, and in most cases, they'll simply give up and move on to someone with weaker protection.
What this actually means for you is that hackers have evolved—ransomware, phishing, and network breaches require multi-layered defenses. Antivirus is just the front door lock, but today’s threats come through the windows, Wi-Fi, and employee inboxes too.
How Much of My Time Will This Take to Manage?
With a managed services partner like Adaptive, your time commitment is almost zero. We handle the 24/7 monitoring, the critical updates, and the immediate threat response so you don't have to.
Our goal is to let you focus completely on running your business, not on becoming a part-time IT expert. We provide clear reports and we're always here to talk strategy, but the day-to-day heavy lifting is our job. It’s a true partnership where we handle the tech, and you handle the business.
Want a real-world look at your current vulnerabilities? Adaptive Information Systems offers a free network risk scan to show you exactly where you stand—no strings attached.
Get a free network risk scan today
Adaptive Information Systems
380 Main St, Salinas CA 93901 | 831-644-0300 | hello@adaptiveis.net
