We are always struck by how serious the after effects of cybercrime can be, for businesses and individuals. Just one successful phishing attack, or an innocent-sounding conversation with a conman, and the result of years of hard work and sacrifice can all be undone in a few minutes.
When we hear these stories, we reflect on what the consequences could be for our business, our family, our colleagues and our clients too. Data theft is growing rapidly in volume and sophistication, with hackers increasingly creating believable phishing emails and impersonating trusted organizations like banks (called social engineering), to trick people into revealing email addresses, usernames and passwords. And with the growth in cloud-based applications, once criminals have these electronic keys, they can access systems and cause havoc at will, from anywhere in the world.
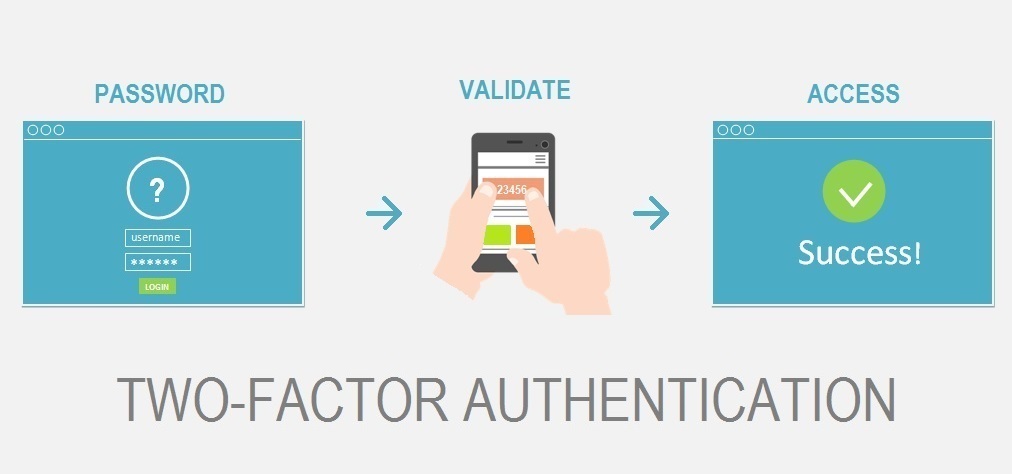
But by taking some simple, extra precautions, we can all make it harder for the attackers and easier to keep the things and people we value safe. There’s one defense that we strongly recommend you apply as widely as possible – Multi-Factor Authentication (MFA). You’re probably using MFA already. When you log in to your online bank, enter your email or username and password, you’re then asked for another code – that’s MFA. It adds an extra security layer, or ‘factor’, on top of usernames and passwords (which, as we know, are often not strong enough), before any access to data is allowed.
Also known as Two-Factor Authentication (2FA), MFA provides a unique, time-limited code via a hand-held device, such SMS text message or app, that is almost impossible for hackers to intercept. Even if the criminal has a stolen email address, username and password, MFA keeps the data safe.
Here’s a quick checklist to get you started on MFA:
- Make a list of everything you and your business access using an email address, username and password
- In particular, identify those systems or services that are cloud or web-based – as they are the ones most at risk of being hacked
- Check with the providers of these systems (or ask your IT support company) to see if MFA can be applied and then do so immediately
If your current provider hasn’t mentioned MFA to you yet, then we would be a bit worried about that! We take security awareness very seriously as part of our proactive support service that keeps our clients’ businesses as safe as possible, and delivers reliable, smoothly-running technology.
Looking for Salinas IT Support Services? Adaptive will manage your business technology needs and implement cyber security best practices so you can focus on running your business.